Topic
This article explains how to use the Tenable integration in NinjaOne.
Environment
- NinjaOne Integrations
- Tenable
Description
Configure Tenable scan integration or import vulnerability comma-separated values (CSV) data into the NinjaOne console. The importer ingests a CSV file containing a list of vulnerabilities identified by a third-party tool. NinjaOne maps the vulnerabilities to managed devices and reports data in the device dashboard. NinjaOne remediates vulnerabilities when you upload new scans that no longer contain previously identified vulnerabilities.
Vulnerability Management for networks and systems is an ongoing, iterative process that requires continuous attention and adaptation to emerging threats and vulnerabilities. It’s a critical component of an organization’s overall cybersecurity strategy, helping to protect assets and data from potential breaches and attacks.
If you need to scan generic vulnerabilities (products other than Rapid7, Tenable, or CrowdStrike), learn how to set up and configure the Vulnerability Importer here.
Please submit feature requests for improvements through our website here.
Index
Select a category to learn more:
Add the Integration
To activate the integration in NinjaOne, perform the following steps:
- Navigate to Administration → Apps → Installed and click Add Apps.
- Select Tenable and click Continue.
- On the Tenable application page, click Enable.
Enabling the application adds the General and Scan groups tabs to the page.
- In the General tab, click Edit for Settings.

- Select Enabled from the Status drop-down menu to capture the behavior of CVEs imported from the integration.
- Select an option from the Impact device health drop-down menu depending on whether you want impacted device health data to appear in the dashboard. If you select Yes, the Device health issues section on the dashboards will update to reflect new data.

- Click Update.
Scan Devices for Vulnerabilities
You must create and manage scan groups in the integration to find CVE data for your devices.
Create Scan Groups
A scan group is a specific selection of items; for example, servers or workstations. Use the Scan groups tab to identify vulnerabilities by reviewing the versions of the operating system and installed applications against the National Vulnerability Database (NVD). The Scan groups tool will identify both traditional managed and unmanaged devices, where endpoints are regularly or continuously assessed for individual vulnerabilities.
- From the application page in NinjaOne, open the Scan groups tab and click Create scan group.

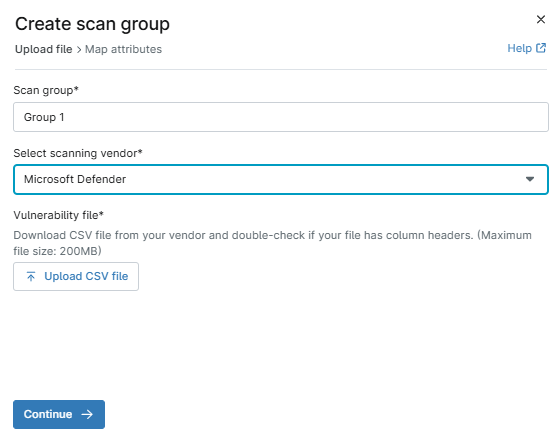
- The Create scan group dialog displays. Enter a unique identifier as a name for Scan group.
- From the Select a scanning vendor drop-down menu, select a scanning vendor. Doing so will help you identify the source of the scanning.
- If you select Other, a new data field will display where you must enter a scanning source name for reference.
- Click Upload CSV file. Navigate to and select a .csv file (limited to 200 MB in size) containing vulnerability data. You can also automate vulnerability uploads from the Automation Library.
- Click Continue to confirm the mapping attributes from the file.
The next page of the dialog allows you to map the attributes. NinjaOne will pull the column data, so the drop-down menus will contain the column header names specific to the file you uploaded.
- From the Map the column that has the Device ID identifier from file* drop-down menu, select the column title that has the device identifier listed in the file.
- A new drop-down menu will appear for Confirm Device ID type*. Select the applicable option.
- In the Map the column that has CVE ID identifier with corresponding vulnerabilities from file* drop-down menu, select the applicable option to identify the column with the CVE ID identifier.
The imported file will publish the associated column data in the importer grid.
If your status is not active, refresh your console to update the status and view the number of vulnerabilities processed from within the file.
Refer to NinjaOne Vulnerability Management: Find CVE Data in NinjaOne for instructions on pulling the data that was scanned in NinjaOne.
Re-Import Scan Groups
Because vulnerability management is ongoing, you may need to update CVE lists to import into the NinjaOne console. To do so, perform the following steps:
- From the application pge in NinjaOne, open the Scan groups tab.
- Move your mouse cursor over a scan group row and click the actions menu. Select Import File.

- The Import file dialog displays. Click Upload CSV file, and then re-import your vulnerability file.
- If needed, refresh the page to view the updates. The data from the most recent import file is always listed.
Delete Scan Groups
To delete a scan group, perform the following steps:
- From the application page in NinjaOne, open the Scan groups tab.
- Move your mouse cursor over a scan group row and click the actions menu. Select Delete group.
Additional Resources
Refer to the Vulnerability Management: Resource Catalog to learn more about vulnerability tools in NinjaOne.