Stronger endpoint security, simpler operations
Protect your endpoints while consolidating tools and reducing complexity
Deliver endpoint security through the familiar NinjaOne platform
Reduce security vulnerabilities
Automated patch and software management improve visibility and control to more quickly identify and remediate patch-based vulnerabilities at scale.
Protect from ransomware
Protect critical business data with real-time monitoring and alerts through endpoint backup. Harden device security to minimize attack surfaces.
Unify IT and security
Reduce silos with integrated security tools that enable seamless security and decrease the time needed to resolve threats.
Customers love NinjaOne
saved time on manual tasks through automation
reduced ticket volumes and resolution times
replaced 3-4 tools with NinjaOne
Features and Solutions
Take control of endpoint security
Gain complete control over end-user devices and set the foundation for endpoint security. Manage applications, remotely edit registries, deploy scripts, and mass configure devices to promote endpoint security.
Role-based access controls
Utilize roles to determine which organizations, features, and functionalities your users can access. Get even more granular with permissions ranging from “no access” to “view, update, create, and delete” to personalize each technician’s access.
Monitor and manage encryption
Manage your AV in one place
Automatically install and manage endpoint protection by configuring when and how your antivirus runs or run ad-hoc scans on individual devices. You have granular control over scan options, schedules, and exclusions.
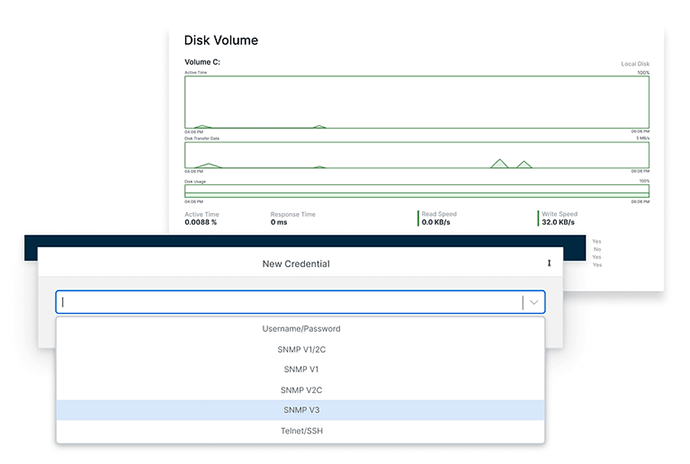
Inject credentials as you need them
Store administrative credentials at the device or organization level with NinjaOne credential exchange and automatically inject them seamlessly when deploying patches, running scripts, or connecting to a device via RDP.
Identify and remove rogue endpoints
Improve onboarding workflows with automatic device approval. Post-onboarding new device approval can be set to manual, elimintating unauthorized machines and operators from leveraging NinjaOne’s internal key and credential exchange for a remote attack.
NinjaOne named a Leader by Gartner®
This is why customers love us
100,000
Endpoints managed
“NinjaOne is a scalable solution. It’s built on a modern SaaS architecture and it’s future-proof.”
40%
More Cost Effective
“NinjaOne’s price point is 40% less than any other endpoint management tool on the market, while being more powerful and easy to use.”
10-15
Tools Replaced
“Before, I needed 10-15 different tools to execute what NinjaOne does in its centralized, single pane of glass.”
30%
Less time for patching
“We observed a 30% reduction in the time taken for patch deployments compared to our previous solution.”
2,000
Endpoints managed
“NinjaOne gives me much more flexibility and security in my work”
30%
Annual ROI
“[NinjaOne] has already shown its value in ROI…it’s at least a hundred thousand dollars annually.”
24x
Faster Endpoint Management
“Our processes have become 24x faster with NinjaOne.”
20-40
Hours Saved Each Week
“Leveraging the automations feature within NinjaOne has enabled me to save upwards of what would likely be 20 to 30 to even 40 hours per week.”
NinjaOne Integrations
Resources
What is meant by endpoint security?
What are the types of endpoint security?
NinjaOne endpoint security includes drive encryption, password management, device approval, antivirus management, and more. Manage applications, remotely edit registries, deploy scripts, and mass configure devices to promote endpoint security.

