Ratings
Acronis
Addigy
Overall
4.8
Meets Requirements
9.2
905 responses
Ease of Use
9.3
912 responses
Ease of Setup
9.4
804 responses
Ease of Admin
9.5
80 responses
Quality of Support
9.4
876 responses
Ease of Doing Business with
9.6
808 responses
Product Direction (% positive)
Based on G2 Winter 2026
Competitors
Acronis
Product Summary
Acronis Cyber Protect Cloud is a cyber protection solution that ensures the security of all business data for MSPs and IT teams. It offers backup, disaster recovery, security, automation, and management capabilities as well as integration with many other tools.
Overall, Acronis empowers providers to deliver reliable services with endpoint management, IT security, and data backup and recovery.
Use Cases
- Endpoint management:
Users of Acronis can monitor, manage, and secure all their endpoints regardless of location. - Data backup and recovery:
Acronis enables IT teams to secure and protect critical data using data backup and recovery. - IT security:
IT professionals can proactively secure their IT environments with EDR, among Acronis’s offered cybersecurity features.
Shortcomings
- Steep learning curve:
According to reviews, it can take a while to fully understand and utilize all of the software’s features and capabilities. - Update/configuration challenges:
Users have reported auto-update failure on agents as well as extra configuration work for integrations with third-party tools. - Support can be improved:
Some users have often found Acronis Cyber Protect Cloud’s customer support to be inconsistent or slow.
Addigy
Product Summary
Addigy is a mobile device management console especially created for Apple devices. It features a full-feature management platform that is specifically made to manage, monitor, and secure iOS, macOS, iPadOS, tvOS-ran devices in real time.
Use Cases
- Support:
Addigy users recognize the platform’s prioritization of delivering good customer support. The platform also has a dedicated community that offers help and can be a source of critical information about its features and services. - Ease of use:
Some users mentioned that Addigy is straightforward to deploy. Its ease of use helps users implement that platform quickly, specifically, those who don’t have that much experience in running a mobile device management software. - Single-login management:
Addigy allows users to manage multiple clients from one login, simplifying the process of applying configurations and policies to all of their clients from a single interface.
Shortcomings
- User interface:
There are users who have raised concerns about Addigy’s user interface. The interface makes some processes a little challenging, such as moving devices between policies. - Limited to Apple:
The platform only supports Apple devices. This can be limiting to MSPs and IT administrators with endpoints on operating systems. - Policy management:
Some users report difficulty understanding how to create and manage policies within Addigy. This affects workflow, requiring extra time to implement policies effectively.
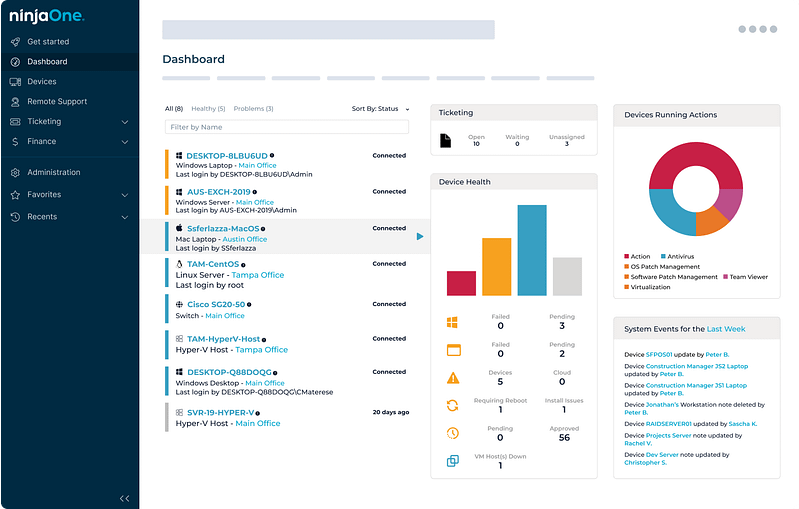
NinjaOne
Why your peers choose us over Acronis and Addigy
For enterprise IT organizations managing complex, distributed environments, NinjaOne delivers where others fall short. Recognized as a Leader in the 2026 Gartner® Magic Quadrant™ for Endpoint Management Tools, NinjaOne is purpose-built to meet the demands of large-scale operations, combining deep visibility, governance-grade control, and the industry’s highest customer satisfaction scores.Enterprise teams choose NinjaOne for its ability to scale without compromise. Whether managing thousands of endpoints across global locations or enforcing consistent security and compliance policies across heterogeneous infrastructure, NinjaOne provides the reliability and operational consistency that enterprise environments require. Unlike many competing solutions that carry steep learning curves and high system resource overhead, NinjaOne delivers enterprise-grade power without the implementation burden.
NinjaOne’s integration ecosystem is built for enterprise breadth, offering pre-built compatibility with leading security and ITSM platforms, enabling organizations to consolidate their toolset rather than work around it. Advanced, role-based reporting and audit-ready dashboards give IT leadership the real-time intelligence needed to drive strategic decisions and demonstrate compliance. For enterprises seeking a proven, scalable endpoint management platform backed by best-in-class support, NinjaOne is the clear choice.
What they're saying
Watch a Demo of the #1 IT Management Software on G2
Related resources
Acronis
Acronis vs JumpCloud
Acronis vs Miradore
Acronis vs Jamf
Acronis vs Moki Total Control
Acronis vs SureMDM
Acronis vs Esper
Acronis vs Addigy
Acronis vs Sophos Mobile
Acronis vs GFI Languard
Acronis vs Lansweeper
Acronis vs Kandji
Acronis vs Mosyle
Acronis vs Cisco Meraki
Acronis vs BMC Helix Client Management
Acronis vs SOTI MobiControl
Acronis vs IBM Security MaaS360
Acronis vs Pandora FMS
Acronis vs Scalefusion
Acronis vs SysAid
Acronis vs VMware Workspace One
Acronis vs Kace
Acronis vs Action1
Acronis vs Syxsense
Acronis vs SuperOps
Acronis vs Matrix42
Acronis vs GoTo Resolve
Acronis vs Level
Acronis vs Bacon Unlimited
Acronis vs ITarian
Acronis vs Hexnode
Acronis vs Baramundi
Acronis vs Automox
Acronis vs Auvik
Acronis vs Goverlan
Acronis vs LogicMonitor
Acronis vs Atera
Acronis vs LogMeIn
Acronis vs ManageEngine Endpoint Central
Acronis vs Microsoft Intune
Acronis vs Bravura Optitune
Acronis vs PRTG Network Monitor
Acronis vs Connectwise Automate
Acronis vs Kaseya VSA
Acronis vs SyncroMSP
Acronis vs SolarWinds Dameware
Acronis vs Panorama9
Acronis vs Veeam
Acronis vs Datto
Acronis vs N-able N-sight
Acronis vs N-able N-central
Acronis vs Naverisk
Acronis vs IT Glue
Acronis vs Ivanti
Acronis vs Pulseway
Acronis vs Arcserve
Acronis vs BigFix
Acronis vs Tanium
Addigy
Addigy vs JumpCloud
Addigy vs Miradore
Addigy vs Jamf
Addigy vs Moki Total Control
Addigy vs SureMDM
Addigy vs Scalefusion
Addigy vs Esper
Addigy vs GFI Languard
Addigy vs Sophos Mobile
Addigy vs LogicMonitor
Addigy vs Goverlan
Addigy vs Auvik
Addigy vs Automox
Addigy vs ConnectWise Automate
Addigy vs PRTG Network Monitor
Addigy vs Bravura Optitune
Addigy vs ManageEngine Endpoint Central
Addigy vs Microsoft Intune
Addigy vs Atera
Addigy vs LogMeIn
Addigy vs Kaseya VSA
Addigy vs Syncro
Addigy vs SolarWinds Dameware
Addigy vs Panorama9
Addigy vs Veeam
Addigy vs Datto
Addigy vs N-able N-sight
Addigy vs N-able N-central
Addigy vs Naverisk
Acronis vs Addigy
Addigy vs Pulseway
Addigy vs Ivanti
Addigy vs IT Glue
Addigy vs Arcserve
Addigy vs BigFix
Addigy vs Lansweeper
Addigy vs Tanium
Addigy vs Bacon Unlimited
Addigy vs Level
Addigy vs GoTo Resolve
Addigy vs Baramundi
Addigy vs Hexnode
Addigy vs ITarian
Addigy vs Matrix42
Addigy vs Kace
Addigy vs Syxsense
Addigy vs VMware Workspace One
Addigy vs SysAid
Addigy vs Kandji
Addigy vs Mosyle
Action1 vs Addigy
Addigy vs SuperOps
Addigy vs BMC Helix Client Management
Addigy vs IBM Security MaaS360
Addigy vs SOTI MobiControl
Addigy vs Pandora FMS
Addigy vs Cisco Meraki
