Endpoints can be found in a variety of industries and settings, but we’ll focus on endpoint devices within IT environments. This article provides a general overview of endpoint devices, their purpose, and how you can better manage and protect them within your organization.
What is an endpoint device?
An endpoint device refers to any device that physically connects to the network and that the network can access. Endpoints are the components located at the end of a communication channel with the network and are used to exchange data back and forth.
Different types of endpoint devices include:
- Desktops
- Laptops
- Workstations
- Tablets
- Mobile devices
- Servers
- Virtual machines
- IoT devices
What is an API endpoint?
An API endpoint is not considered a traditional IT endpoint. An API is a gateway which allows for the passing of information between two systems. Some APIs will even allow you to connect to outside pieces of software or outside integrations, which is often how software solutions with outside integrations accomplish this. An API is a connection application that allows data to travel back and forth, but it is not a physical endpoint. Even though APIs are not physical endpoints, it’s still important to follow the latest API security best practices to ensure that your data remains protected.
Learn the basics of API management with NinjaOne’s comprehensive guide.
What is not an endpoint device?
Other common IT devices that are not endpoints include input devices and infrastructure devices. Infrastructure devices, which consist of a server, router, network interface controller (NIC) switch, hub, and modem, are used directly for network monitoring.
Essentially, any intermediary device is not considered an “endpoint”, as it only transmits a conversation between two devices. As its name suggests, an “endpoint” needs to be the end result of communication between devices.
Nevertheless, there are always exceptions to the rule. A router, for example, can possibly be considered an endpoint device when:
- It allows users to configure their settings on a web interface.
- It runs network services that communicate with other devices.
- It is part of a mesh, peer-to-peer, or VPN network that uses end-to-end encryption.
It’s worth noting, though, that these considerations are rare and have limitations. Thus, for all intents and purposes, it’s better to consider all routers as customer-premise equipment (CPE) rather than endpoint devices.
Other network devices not usually considered endpoint devices are load balancers and storage area networks.
What is the purpose of an endpoint device?
Endpoints are computers that enable users to enter, receive, or manipulate information. Without endpoints, users would have no direct way of communicating with the network or accessing data from it. They communicate information to and from the network.
Within a business, endpoint devices are used for productivity purposes and to control or manipulate business operations actively. These devices are essential for members of an organization to complete their job responsibilities and are typically the main tool that they use, so it’s important to keep endpoints healthy and secure. A process designated for this very purpose is endpoint management.
What is endpoint management?
Endpoint management consists of monitoring, remediating, and securing the endpoints in an IT environment. The number of endpoints within organizations continues to grow, with enterprises managing an average of 135,000 endpoints.
It is essential for a business to keep track of any endpoints connected to its network. A healthy endpoint contributes to the well-being and the overall success of an organization’s IT environment, while an unhealthy and vulnerable endpoint can be the gateway for a whole host of issues that may snowball into the rest of the business.
How does endpoint management work?
Endpoint management can occur either on-premises or remotely. However, cloud-based remote management has increased in popularity due to its convenience and ease-of-use. Gartner predicts that more than 90% of clients will be using a cloud-based endpoint management tool by 2025.
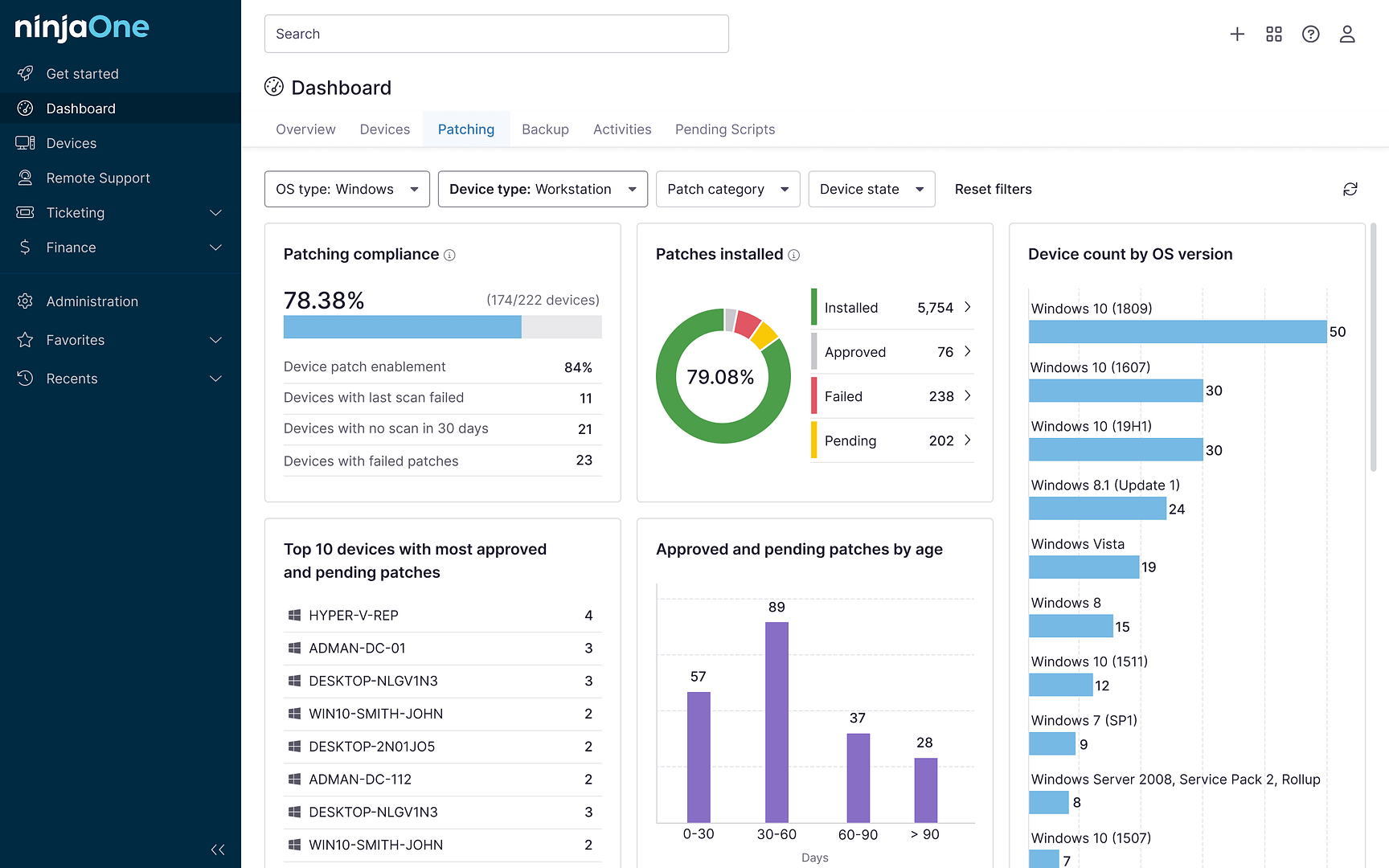
The process of endpoint management works by, first, locating all endpoints within an organization. With NinjaOne, these endpoints then have an agent placed on them. This allows you to effectively access and control various monitoring and maintenance actions on an endpoint. Once endpoints have the agent installed, then they will be able to connect to your central endpoint management console. From the console, you are able to complete monitoring and management tasks in a unified, single-pane-of-glass display.
Importance of securing endpoint devices
According to Statistica, the global endpoint security market is projected to reach over $16B in 2024 and is expected to grow in the coming years. This is further emphasized in the latest “Guide to Endpoint Security Concepts” by Gartner Research, which claims that endpoint devices are often the most vulnerable aspect of any IT estate because of the complexities involved in securing them. Think about it: There are many different endpoint devices, each with various operating systems and types. It’s virtually impossible to secure all of them properly.
This is what cybercriminals try to exploit. From a criminal standpoint, successfully attacking an endpoint could potentially lead to a compromised IT network, ultimately leading to more significant financial gain. Ransomware, in particular, has the potential to become the much-needed entry point to an otherwise secured corporate network.
As cyber attackers become more sophisticated, traditional antivirus software is no longer enough to mitigate the risk of your endpoints being exploited. It is vital that your business adopts a more proactive and comprehensive approach toward endpoint management and security.
Endpoint security is among the top 5 IT security fundamentals every business leader must know.
→ Download our free guide today.
5 best practices for endpoint management
1. Manage all organizational endpoints
The endpoint management process is most effective if you ensure that every single endpoint device is accounted for, monitored, and managed. When you initially set up endpoint management software, systematically identify all endpoints within your business, and ensure you have software set up to discover new endpoint devices.
2. Monitor in real-time
Real-time endpoint data lets you know exactly what’s currently happening on an endpoint at any given point in time. You can monitor the health, security, and efficiency of your endpoints to support optimal performance and protect them from potential malicious cyber threats.
3. Maintain full visibility
Make sure that you can see the status of all your endpoint devices in one location, such as a unified console. This gives you quick information about endpoints in your IT environment without having to switch back and forth between screens.
4. Apply automation where possible
Since there’s typically lower stakes involved when handling endpoints, endpoint management thrives off of IT automation. Automate patch management, endpoint maintenance, software deployment, and more using an endpoint management solution like NinjaOne.
5. Remediate issues promptly
One issue on an endpoint device can have a snowball effect and cause a variety of other issues, so it’s important to remediate issues promptly when they’re identified. Endpoints also serve as a gateway to your entire network, so it’s important to ensure they’re in good health and protected so threat actors can’t take advantage of a weak system.
How can endpoint devices be protected?
Because endpoints give users direct access to your organization’s IT network, they pose a security risk to your entire IT environment. If one of the endpoints somehow got into the hands of a threat actor, that attacker could potentially wreak havoc on your entire business. The World Economic Forum found in its recent Insight Report that 54% of organizations have an insufficient understanding of cyber vulnerabilities in their supply chain. This may have contributed to 41% of these companies reporting suffering from a material incident in the past 12 months.
Endpoints can be protected through endpoint security. Endpoint security is the process of protecting your endpoints through device hardening, vulnerability mitigation, and securing the OS. Learn more about specific actions you can take to improve your endpoint security process.
Endpoint security challenges
- Lack of visibility. It is important that you work with a trusted endpoint management company like NinjaOne to gain complete visibility into your entire IT infrastructure. This helps you detect and remediate threats as soon as possible.
- Limited resources. Endpoint management can be resource-intensive, especially when managing a lot of assets. It is highly recommended that you work with a vendor that provides a lightweight yet reliable solution.
- Complexity. If you are a larger IT enterprise, endpoint security can become complex.
- Ever-evolving threat landscape. Every day, cyber criminals look for new ways to exploit vulnerabilities in your endpoint devices.
Endpoint security strategies
Businesses of all sizes must create an extensive endpoint security strategy based on their specific needs, overall goals, and IT budget. Still, some key components should be considered.
- Security controls, including anti-malware software, firewalls, and intrusion detection systems. Also, consider evaluating the benefits of the principle of least privilege so users only have access to the necessary tools to do their jobs.
- Use multi-factor authentication (MFA). MFA is a simple but excellent way to improve endpoint security. It significantly reduces the risk of unauthorized access and adds an extra layer of security to all your endpoints.
- Endpoint detection and response (EDR) solutions may strengthen your security strategy. NinjaOne offers a free 26-page guide on everything you need to know about EDR here.
- Proactive patch management. Regularly updating your operating systems and business applications contributes to good cyber hygiene, leading to better endpoint security.
- Regular risk assessments help you identify weaknesses in your current strategies and areas of improvement.
- Clear BYOD policy. More and more companies follow BYOD policies that allow employees to use their own computers, smartphones, and other devices for work. Ensure that their devices (and inevitably your company data!) are properly secured to prevent an attack.
- Employee training. Include all team members in your organization, from rank-and-file employees to C-level management.
How to build a great endpoint security strategy
- Identify your business assets. You don’t know what you don’t know. The first step in building an effective endpoint security strategy involves identifying your most valuable assets and the level of protection each of them needs.
- Understand your threat profile. Determine the most appropriate security solutions for each identified asset. (Remember to consider your budget).
- Design a layered security approach. Implementing multiple layers of security to reduce the risk of attack is highly recommended.
- Test and evaluate. Regularly test and validate your endpoint security strategy to ensure it adequately protects your network.
Manage your organizational endpoints using NinjaOne
NinjaOne’s comprehensive endpoint manager simplifies and streamlines how you monitor and manage your organizational endpoints. It is 100% cloud-based and consolidates many of IT teams’ products or tools into one solution.
If you’re ready, request a free quote, sign up for a 14-day free trial, or watch a demo.