Key Points:
- Patch management lifecycle: A structured process IT teams follow to identify, test, deploy, and verify software patches.
- 10 lifecycle stages: The process covers identification, prioritization, policy creation, monitoring, testing, approval, modifications, deployment, auditing, reporting, and repetition.
- Lifecycle benefits: Strengthens security, reduces downtime, improves compliance, lowers IT costs, and increases efficiency.
- Lifecycle challenges: Time constraints, incomplete IT inventories, patch failures, unsolved risks, and the ongoing catch-up cycle.
- NinjaOne advantage: Automates many lifecycle stages, helping IT teams reduce complexity and improve consistency. Keep in mind, though, that manual configuration is still needed for some stages.
The patch management lifecycle is the structured, repeatable process IT teams use to identify, test, deploy, and verify software patches across their environment. Following a clear lifecycle ensures MSPs and IT enterprises can strengthen security, minimize downtime, and maintain compliance without letting security vulnerabilities slip through the cracks.
In this guide, we’ll break down the stages of the patch management lifecycle, explore common challenges, and show how automation can streamline the process for IT professionals.
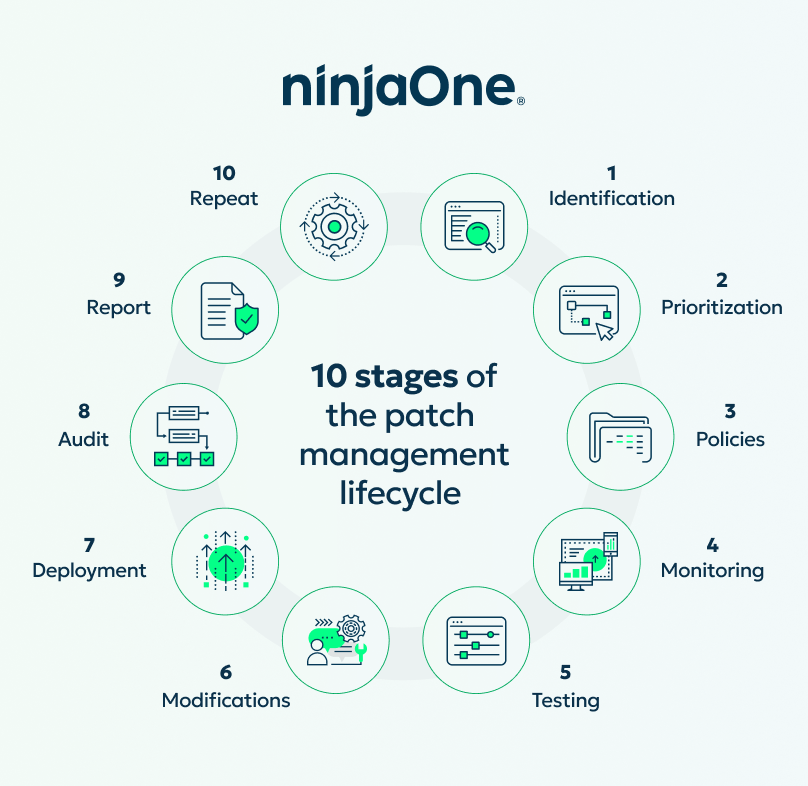
10 stages of the patch management lifecycle
A complete patch management lifecycle shows the entire patch management process. While this list shows all the steps separately, some organizations choose to combine certain stages together. A complete patch management lifecycle includes these 10 stages.
Each stage comes with its own challenges, but with NinjaOne Patch Management, IT teams can simplify, automate, and optimize every step along the way.
🛑The names and order of these stages can vary across IT practices. This document should be understood as a practical guide, not a strict standard.
Stage 1: Identification
Before implementing a patch management process, an organization needs a network inventory, which identifies all IT assets on a network. To build a comprehensive network inventory, a team will need to conduct a thorough network inspection using network assessment software.
✅ How NinjaOne can help: NinjaOne automatically discovers and inventories endpoints, giving IT teams complete visibility into what devices and applications require patching.
Stage 2: Prioritization
After conducting a network assessment and understanding the current IT environment, a team can then prioritize vulnerabilities and threats that were uncovered during the inspection. Categorize users and/or systems by risk and priority to create more targeted patching policies in the following steps.
✅ How NinjaOne can help: NinjaOne allows you to categorize endpoints and create custom patching policies based on severity, risk level, or business priority. This ensures that the most critical systems and applications receive patches first, aligning patch deployment with organizational needs.
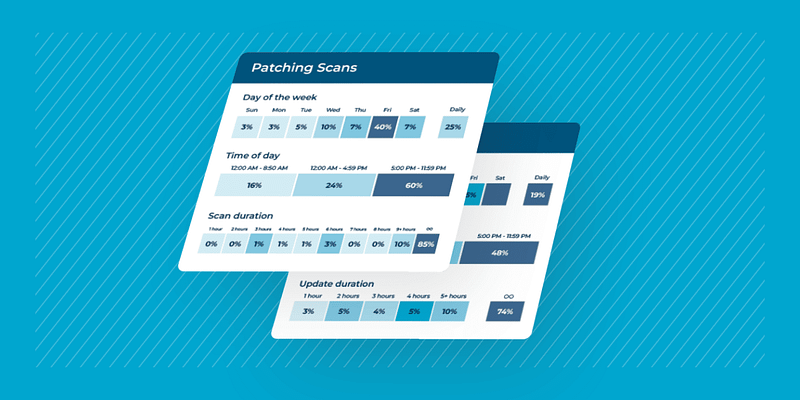
Stage 3: Policies
With users and/or systems effectively categorized, an organization can now create patch management policies. Creating an effective and scalable patching policy is a simple and straightforward process that allows users to set up and manage patching requirements with ease. These patching requirements, or criteria, determine what needs to be patched when it needs to be patched, and under what conditions to patch.
✅ How NinjaOne can help: NinjaOne enables IT teams to define patch approval rules, schedules, and escalation workflows automations to ensure consistency across the environment.
Stage 4: Monitoring
In this stage, a team will be on the lookout for new patches and vulnerabilities from vendors. Usually, organizations will set up a system to receive notifications about upcoming patches and vulnerability updates from vendors instead of keeping track manually.
✅ How NinjaOne can help: NinjaOne continuously monitors vendor updates and vulnerability feeds, so admins are alerted to new patches without manual tracking.
Stage 5: Testing
To test patches, an IT team usually uses a test environment that allows them to catch unexpected issues before the patches roll out. Before moving to the next stage in the patching lifecycle, an organization should ensure that patches roll out successfully to the test environment and that the patches operate as they are supposed to.
⚠️ Note: Keep in mind that part of the testing process is having someone approve the patches before they go live. Even with the best automation, a human touch is important to ensure accuracy and relevance.
✅ How NinjaOne can help: NinjaOne lets you deploy patches first to pilot groups or test segments, ensuring they are validated in a controlled environment before being rolled out more widely.
Stage 6: Modifications
Documentation is tedious, but it’s necessary to keep the entire IT team, and other members within an organization, on the same page. Note any changes about to be made with patches before deployment.
✅ How NinjaOne can help: NinjaOne automatically documents patch activity, providing logs and reports that keep teams aligned and audit-ready.
Stage 7: Deployment
Now, it’s time to deploy patches in accordance with the patch management policies established in stage three. During this stage, IT teams verify whether deployments are successful and identify if adjustments are required.
✅ How NinjaOne can help: NinjaOne automates patch deployment across operating systems and third-party apps, reducing manual work and speeding up rollouts.
Stage 8: Audit
Pending or failed patches can sometimes arise after deployment. Monitor these problems closely for incompatibility or performance issues and advise end-users of the issues and upcoming solutions if necessary.
✅ How NinjaOne can help: NinjaOne tracks patch success and failures in real time, giving IT teams the ability to remediate issues quickly.
Step 9: Report
A patch compliance report provides execs and other departments with visibility into the organization’s IT infrastructure and the impact of patching. These reports can be scheduled on a regular basis, such as monthly, to maintain ongoing oversight.
✅ How NinjaOne can help: NinjaOne provides customizable patch compliance and executive reports that can be scheduled or generated on demand.
Step 10: Repeat
The final stage of the patch management lifecycle is to review, update, and repeat steps one through nine. This will keep information up-to-date and accurate, allowing an IT team to refine and optimize all patch management processes.
✅ How NinjaOne can help: NinjaOne supports recurring patch cycles via automation and continuously refreshed reporting, helping make patching more consistent and repeatable with reduced manual effort.
Why a patch management lifecycle matters
When an organization has a clear understanding of a patch management lifecycle, its IT team is able to improve each stage for optimal performance. In addition, following a step-by-step patch management lifecycle helps organizations strengthen security, reduce downtime, and improve compliance by applying a structured, repeatable approach.
For a broader look at what patch management is and how it supports IT operations, see our guide on What is Patch Management? Definition, Benefits, & Best Practice.
Patch management lifecycle benefits and challenges
| Benefits of a patch management lifecycle | Challenges of a patch management lifecycle |
| Strengthens security posture by closing vulnerabilities | Teams may spend hours per week managing patching |
| Reduces downtime and disruption through structured testing and staged deployment | Requires a complete IT inventory, which many organizations lack |
| Helps organizations meet regulatory and compliance requirements | Some vulnerabilities may remain unresolved, creating ongoing risk |
| Lowers IT costs by preventing breaches and emergency remediation | Patch failures can disrupt systems or cause downtime |
| Improves efficiency with automation and consistency | Patching remains a catch-up game as new vulnerabilities constantly appear |
5 key benefits of a patch management lifecycle
- Stronger security posture
A patch management lifecycle ensures that vulnerabilities are consistently identified, prioritized, and resolved. By closing security gaps in a structured way, organizations significantly reduce their attack surface. Since threat actors often target known vulnerabilities, timely patching through a repeatable lifecycle is one of the most effective defenses against breaches and ransomware.
- Reduced downtime and disruption
Unpatched systems are more likely to fail or experience performance issues. By incorporating testing, staging, and deployment into the lifecycle, IT teams can reduce the risk of downtime caused by both unpatched vulnerabilities and failed patches. This proactive approach helps keep business operations running smoothly with fewer interruptions.
- Easier compliance with industry regulations
Many regulatory frameworks, such as HIPAA, PCI-DSS, and GDPR, require organizations to apply security updates within strict timelines. A formal lifecycle provides the documentation, processes, and reports needed to demonstrate compliance. This not only simplifies audits but also builds confidence with clients, partners, and stakeholders.
- Lower IT costs by preventing breaches
The financial and reputational damage caused by a data breach often dwarfs the investment in proactive patching. A patch management lifecycle helps organizations address vulnerabilities before they can be exploited, lowering the risk of costly incidents. Over time, this structured approach reduces emergency remediation expenses and protects long-term business continuity.
- Improved efficiency through automation and consistency
A structured process allows IT teams to automate routine steps, apply patches at scale, and track progress in a repeatable way. This improves efficiency, reduces human error, and frees IT staff to focus on higher-value projects rather than firefighting.
5 patch management lifecycle challenges
A step-by-step patch management process can help solve pesky patch management challenges that hinder your IT department.
For additional guidance, check out our list of the top 10 patch management challenges of 2025.
- Time
Many IT teams still grapple with how long patching takes. A recent IDC study found that 70% of IT teams spend over six hours per week managing security patches, which adds up to nearly a full workday dedicated just to this task (Canonical). To improve efficiency, teams are increasingly turning to automation to cut manual work and speed up the patching process.
- IT inventory
Too often, IT teams do not have a complete IT inventory to reference for patching. Without full visibility into endpoints, servers, and applications, it’s easy for vulnerabilities to slip through the cracks. That’s why it’s important to complete an IT asset inventory.
- Unsolved risks
Since patching focuses on fixing the most troublesome vulnerabilities first and saving the others for later, the patching process often leaves vulnerabilities and other issues unsolved. This leaves systems vulnerable to attack, thus weakening security and increasing risks.
- Patch failures
Updating software is risky, and patch failures can cause numerous problems for an organization. According to Gitnux, 75% of organizations fail to apply patches promptly, leaving systems exposed to known vulnerabilities.
- Vulnerability management
Even organizations with the best patching and vulnerability management processes run into vulnerabilities. Unfortunately, patching is a catch-up game, so as soon as an IT team patches one vulnerability, another could pop up at any time.
Differences between vulnerability management and patch management
Vulnerability management and patch management are both similar processes, but they are not the same. We found that there are plenty of core differences between patch management and vulnerability management even though the two terms are often used interchangeably.
Vulnerability management is the process of identifying, analyzing, reporting, and fixing cybersecurity threats, while patch management is the process of creating and applying patches to fix flaws or update a product or service with new features.
Why a patch management lifecycle matters
When an organization has a clear understanding of a patch management lifecycle, its IT team is able to improve each stage for optimal performance. In addition, following a step-by-step patch management lifecycle allows organizations to take advantage of the many benefits of effective patch management.
To recap:
Vulnerability management is the ongoing process of identifying, analyzing, reporting, and prioritizing cybersecurity threats across an IT environment. It takes a broad view of risk, addressing not only missing patches but also misconfigurations, outdated systems, and potential zero-day exploits.
Patch management, on the other hand, is a more focused process. It specifically involves creating and applying patches to fix flaws, close known vulnerabilities, or update a product or service with new features. While patch management is often a subset of vulnerability management, the two serve different but complementary roles in a security program.
In other words, vulnerability management finds and prioritizes risks, while patch management remediates those risks through updates. Both are essential for maintaining a strong cybersecurity posture.
We’ve created this table to highlight the differences in an easy-to-understand way:
| Aspect | Vulnerability management | Patch management |
| Definition | Identifies, analyzes, reports, and prioritizes security weaknesses across IT systems | Applies patches and updates to remediate vulnerabilities and improve functionality |
| Scope | A broader scope and covers all vulnerabilities, including configuration issues and zero-days | Has a narrower scope and focuses on addressing known vulnerabilities through patches |
| Primary goal | Reduce risk exposure by understanding threats and weaknesses | Eliminate specific vulnerabilities by updating software, operating systems, and apps |
| Process | Continuous scanning, assessment, and prioritization | Testing, deployment, auditing, and reporting of patches |
| Tools commonly used | Vulnerability scanners, threat intelligence platforms | Patch management solutions, RMM platforms, OS, and vendor update tools |
Overcome patching challenges with NinjaOne
One of the best ways to overcome patching challenges is to automate processes with NinjaOne’s patch management software. With NinjaOne’s patching solution, you can automate processes, remediate vulnerabilities, and gain insight into your entire IT portfolio from a single pane of glass. Sign up for your free trial to start optimizing every stage of your patch management process.