Key points:
- Define DSPM: Data security posture management (DSPM) is a security approach that discovers and assesses risk across data in cloud and on-prem environments.
- Unify Data Visibility and Risk Prioritization: DSPM consolidates data discovery, classification, risk assessment, and compliance monitoring into a single platform.
- Secure Data Across Environments: DSPM provides unified visibility across multi-cloud, hybrid, SaaS, and AI data sources.
- Automate Risk Detection and Response: Modern DSPM tools monitor data access, permissions, and movement to detect misconfigurations and anomalous behavior.
- Enable Continuous Compliance Monitoring: DSPM supports real-time compliance with regulations and standards such as GDPR, NIS2, and ISO/IEC 27001:2022.
- Identify When DSPM Is Required: Organizations adopt DSPM when data sprawl, SaaS usage, and regulatory pressure outpace manual security processes
Managing data security used to mean playing detective across dozens of disconnected systems. Data security posture management (DSPM) changes that game entirely. Instead of hunting for vulnerabilities and compliance gaps, you get
- automated discovery,
- continuous monitoring,
- and actionable insights that actually help you stay ahead of threats.
What is DSPM and why does it matter for IT teams?
Data security posture management represents a unified approach to discovering, classifying, and protecting sensitive data across your entire digital infrastructure.
Essentially, DSPM is a combination of automated data discovery with continuous risk assessment that provides full visibility into your organization’s data security landscape.
Rather than managing separate tools for
- data classification,
- vulnerability scanning and
- compliance monitoring
DSPM consolidates these functions into a single platform that eliminates the need for manual coordination between disparate security systems.
Beyond that, this process involves risk prioritization based on business impact as well as the coverage of structured and unstructured data such as the following:
- SaaS apps (e.g., M365, Google Workspace, Salesforce)
- Data warehouses (e.g., Snowflake, BigQuery)
- GenAI training data and prompts
Enforce data security standards consistently with IT automation.
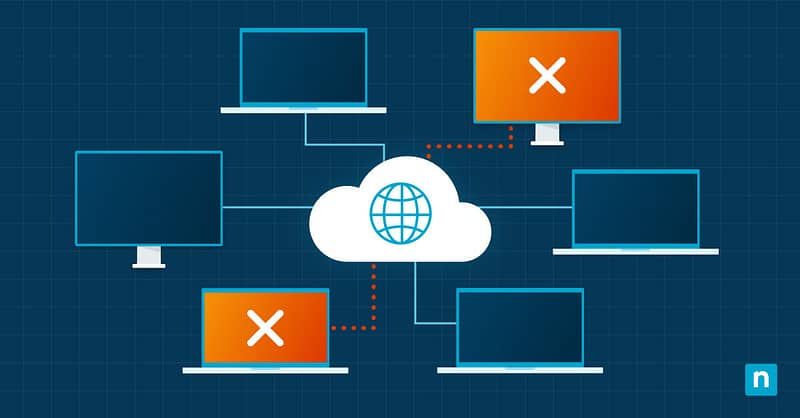
Data security posture management in cloud security
DSPM excels in cloud environments where data can spread across multiple platforms, services, and geographic regions. Traditional cloud security tools often create blind spots between different cloud providers or fail to track data as it moves between on-premises and cloud storage.
On the other hand, DSPM addresses these gaps by
- providing unified visibility across hybrid and multi-cloud architectures,
- automatically mapping data flows and
- identifying security risks regardless of where your information resides.
This cloud security strategy provides consistent protection whether your data lives in AWS, Azure, Google Cloud, or your private data center, along with
- SaaS collaboration tools,
- API-connected business apps, and
- AI pipelines and LLM usage.
How DSPM supports IT security best practices
Keeping systems under constant watch and responding automatically to threats is necessary, yet it’s something manual work simply can’t scale. With DSPM, the repetitive parts of security are automated allowing your team to move faster while still meeting the standards you rely on.
Improve visibility and control over sensitive data
Sensitive data includes
- personal information,
- financial records,
- intellectual property,
- healthcare data and
- confidential business communications
all of which require special protection. DSPM platforms automatically scan your entire infrastructure to locate and classify these data types, creating detailed inventories that update in real-time as new information enters your systems.
Key visibility improvements include the following:
- Automated discovery of sensitive data across all environments: databases, file shares, cloud platforms, and backups
- Real-time classification of data types, sensitivity levels, and compliance obligations without manual tagging
- End-to-end data flow mapping that reveals how information moves across systems, apps, and user roles
- Access monitoring and audit trails that track who views, edits, or deletes sensitive data and when
- Dynamic inventory updates that detect and classify new data sources as they appear, ensuring your visibility current
Automate risk detection and response
DSPM continuously analyzes your data environment to identify potential security risks, misconfigurations, and compliance violations without requiring manual investigation. These systems monitor access patterns, permission changes, and data movement to detect anomalies that might indicate security threats or policy violations.
Advanced DSPM tools integrate with existing security tools to trigger automated responses when high-risk situations arise, such as quarantining alerting security teams when unauthorized access attempts occur.
This automation eliminates the detective work that consumes significant IT resources while providing faster response times.
Enable real-time compliance monitoring
Traditional compliance management relies on periodic audits and manual reporting processes that create gaps between assessment cycles. Meanwhile, DSPM transforms compliance monitoring into a continuous process that provides real-time visibility into your organization’s adherence to regulatory requirements such as the following:
These platforms can automatically generate compliance reports, track remediation efforts,, and alert teams when configuration changes create new compliance risks. Real-time monitoring capabilities provide immediate attention to compliance violations rather than waiting for the next scheduled audit cycle.
When to implement data security posture management
Organizations typically consider DSPM implementation when their existing security tools fail to provide comprehensive visibility across increasingly complex IT environments. The decision to adopt DSPM often coincides with
- digital transformation initiatives,
- cloud migrations, or regulatory compliance requirements
that exceed the capabilities of traditional security approaches.
Signs that your organization needs DSPM
If manual security processes are draining resources, compliance demands are outpacing your capabilities, or data sprawl is creating blind spots across your infrastructure, it’s time to consider DSPM. Organizations experiencing rapid growth, cloud adoption or regulatory changes often find that their existing security tools cannot keep pace with evolving requirements.
DSPM implementation timing depends on recognizing these key indicators:
- Security teams spend more time hunting for data and vulnerabilities than addressing actual threats or implementing protective measures.
- Compliance audits reveal data protection gaps that existing tools failed to identify or address adequately.
- Data breaches occur because sensitive information exists in unknown or unmonitored locations across your infrastructure.
- Manual processes delay incident response times and hinder proactive threat mitigation efforts
Integrate DSPM with existing cloud security tools
DSPM delivers the most value when it integrates seamlessly into your existing security stack without adding complexity, tool sprawl or new operational overhead. The top DSPM platforms integrate directly with the cloud security, SIEM and identity tools you already use, which helps streamline your workflows and reduce administrative work.
Look for solutions that strengthen your current security stack, rather than requiring you to replace what’s already working. This way, you consolidate security functions and avoid piling on more management overhead.
Learn how NinjaOne Endpoint Management supports secure, compliant endpoint environments. Explore the FAQs for more information.
Avoid common mistakes in DSPM adoption
Teams often underestimate how much planning goes into a smooth DSPM rollout, which leads to delays and disappointing results. Common mistakes include the following:
- Trying to deploy DSPM everywhere at once instead of rolling it out in phases, testing, and making adjustments along the way.
- Not bringing in the right stakeholders, especially data owners and business users who know how sensitive information moves through daily work.
- Overlooking the need for clear data classification policies before turning on DSPM tools, which can lead to inconsistent or unreliable automated results.
Endpoint security breaks down without reliable visibility and control.
Key questions to ask before choosing a DSPM solution
Selecting a DSPM platform isn’t just about checking off features, you want a solution that fits your business’s current and future needs. Before you commit, step back and look at the bigger picture — how will this platform integrate with your existing tools and what will it look like as your organization grows?
Consider these key questions:
- Does the platform provide comprehensive coverage across your current and planned infrastructure, including on-premises systems, multiple cloud providers, and hybrid environments?
- How effectively does the solution integrate with your existing security tools, particularly SIEM systems, identity management platforms, and IT security best practices already in place?
- What level of automation does the platform offer for data discovery, classification, risk assessment, and compliance reporting without requiring extensive manual configuration?
- Can the solution scale to accommodate your organization’s growth while maintaining performance and providing detailed visibility into expanding data environments?
- Does the vendor provide adequate support, training, and professional services for successful implementation and ongoing DSPM optimization?
Align your data security strategy
Increase visibility and reduce data risk as well as a automate patching, backups and threat protection all in one platform that integrates with your existing tools and scales with your business. No platform fees. Free onboarding. Local support. Start your free trial and see how NinjaOne can accelerate your DSPM strategy.
Quick-Start Guide
Data Security Posture Management (DSPM) is a comprehensive approach to protecting sensitive data across cloud and on-premises environments. It focuses on:
1. Data Discovery: Identifying and locating sensitive data across different platforms
2. Classification: Categorizing data based on sensitivity and type
3. Monitoring: Continuously tracking data access, movement, and potential risks
4. Protection: Implementing safeguards to prevent unauthorized access or breaches
Key Features:
– Continuous assessment of data security risks
– Sensitive data identification (PII, PHI, PCI)
– Risk mitigation
– Compliance support
– Enhanced data protection
How NinjaOne Relates:
While NinjaOne doesn’t have a dedicated DSPM solution, it offers complementary security features:
– Vulnerability Management
– Patch Management
– Integration with security tools
– Device health monitoring
Recommendation:
For comprehensive DSPM, you might want to consider specialized DSPM solutions that can integrate with NinjaOne’s existing security tools. The ideal approach would be to use NinjaOne for endpoint and vulnerability management while supplementing it with a dedicated DSPM solution for data-centric security.