NinjaOne Endpoint Security for Linux: Fortifying Your Digital Fortress
Enhance Linux security with confidence using NinjaOne Endpoint Security — ensuring strong protection, proactive threat detection, and efficient management for maximum security.
Enhance Linux security with confidence using NinjaOne Endpoint Security — ensuring strong protection, proactive threat detection, and efficient management for maximum security.
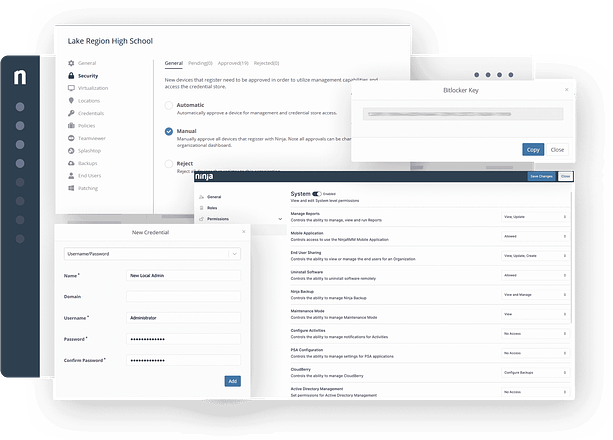

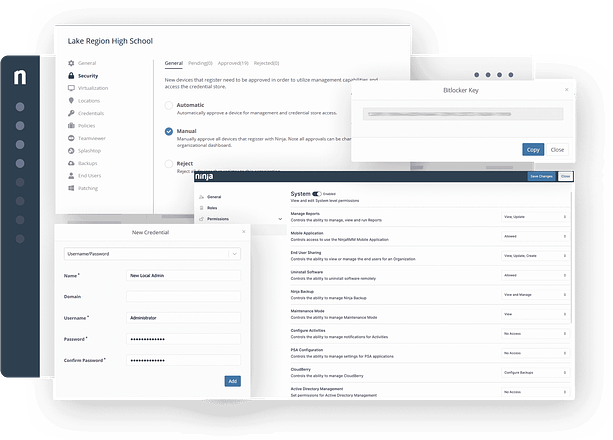
Unified endpoint management under a single pane of glass simplifies your IT landscape, boosting visibility and control.
Automated tasks, centralized management, and remote device control streamline IT operations, freeing up resources for strategic projects.
Proactive threat detection, vulnerability management, and a layered defense approach mitigate security risks and minimize attack surfaces.
Adapt to your evolving needs with a solution that scales effortlessly and caters to any organization size or infrastructure complexity.
100,000
Endpoints managed
“NinjaOne is a scalable solution. It’s built on a modern SaaS architecture and it’s future-proof.”
40%
More Cost Effective
“NinjaOne’s price point is 40% less than any other endpoint management tool on the market, while being more powerful and easy to use.”
10-15
Tools Replaced
“Before, I needed 10-15 different tools to execute what NinjaOne does in its centralized, single pane of glass.”
30%
Less time for patching
“We observed a 30% reduction in the time taken for patch deployments compared to our previous solution.”
2,000
Endpoints managed
“NinjaOne gives me much more flexibility and security in my work”
30%
Annual ROI
“[NinjaOne] has already shown its value in ROI…it’s at least a hundred thousand dollars annually.”
24x
Faster Endpoint Management
“Our processes have become 24x faster with NinjaOne.”
20-40
Hours Saved Each Week
“Leveraging the automations feature within NinjaOne has enabled me to save upwards of what would likely be 20 to 30 to even 40 hours per week.”
Linux endpoint security is the practice of protecting Linux-based devices against threats such as malware, unauthorized access, and data breaches. It is essential because Linux systems often run critical infrastructure and servers, making them attractive targets for attackers.
Linux endpoints refer to computing devices such as desktops, laptops, servers, and specialized hardware that operate on the Linux operating system. These endpoints play various roles within a networked environment, serving as user workstations, data servers, or specialized nodes. Linux endpoint security involves implementing measures like firewalls, antivirus software, access controls, and encryption to protect these devices from cyber threats, ensuring the integrity and functionality of Linux-based systems in diverse computing scenarios.
Linux endpoint security employs a multi-layered approach to safeguard systems. This includes firewalls for network control, antivirus software to detect and remove malware, intrusion detection systems for monitoring, access controls to restrict unauthorized access, regular updates to address vulnerabilities, encryption for data protection, behavioral analysis to identify anomalies, and endpoint detection and response for real-time monitoring and incident response. Together, these measures create a robust defense against cyber threats on Linux-based systems.