Key Points
- Patch compliance ensures all systems and software remain up to date with approved patches to reduce vulnerabilities and maintain regulatory standards.
- Regular compliance reports help IT teams track missing patches, identify non-compliant endpoints, and maintain full visibility across devices.
- Effective patch compliance depends on accurate asset inventory, risk-based patch prioritization, and clear patching policies.
- Measuring patch compliance involves tracking patch deployment success rates and reporting compliance levels against internal or industry benchmarks.
- Cross-platform and remote device support are essential for maintaining consistent patch compliance across Windows, macOS, and Linux environments.
Many high-profile cyberattacks could be minimized or avoided altogether if not for unpatched software. This is why patch management is a crucial part of cybersecurity best practices and is widely recognized by compliance frameworks around the world.
As security regulations evolve, new standards for patch management are also rolled out. This means end users and IT professionals will need to take a serious look at their patching practices, not just to stay compliant, but for their own security.
With that in mind, this guide offers key considerations and insights for establishing a patch management strategy that can scale with your organization.
What is patch compliance?
A patch compliance audit will examine the number of devices on your network that are compliant, which refers to the machines that have been successfully patched and have current updates to protect them against threats. Patch compliance is also a broad concept, not only applying to those machines but also the measures an organization uses to detect and install new patches,the level of insight it has into its endpoints (devices), and how often it ensures that all software and hardware is up to date.
There are many variables that can affect the success of patch deployment, particularly in larger IT environments with many devices. Fortunately, there are quite a few solutions organizations can use to ensure they’re patching correctly and that all devices and systems are compliant.
💡 Tip: You can also watch our video on What is Patch Compliance to explore this topic in another format.
Patch management in compliance frameworks
In a bid to safeguard data and privacy, several government institutions and agencies have developed cybersecurity standards (and more are certain to come). Within these frameworks, patch compliance is always required — a testament to its importance in the bigger cybersecurity picture. Some of the most prominent compliance standards include:
- PCI (Payment Card Industry Data Security Standard): These security regulations govern the technical and operational standards that businesses must use to secure their customers’ credit card information.
- HIPAA (Health Insurance Portability and Accountability Act): These security and privacy standards apply to healthcare businesses and help to keep patient data from being leaked, stolen, or tampered with.
- GDPR (General Data Protection Regulation): This EU regulation is designed to protect the data and privacy of its citizens and includes strict patching protocol as part of its security standards.
Effective patch management must be aligned with industry and legal standards to protect sensitive data and reduce business risks at scale. Compliance is a minimum baseline, not true security. Meeting standards satisfies audits (e.g., 30-day critical patching), but real security requires addressing lower-severity issues and implementing controls that exceed mandates.
Common challenges in meeting patch compliance
Patch compliance can be difficult to nail down as there can be so much variance between IT environments, use cases, and industry sectors. On that note, there are still common pitfalls that you can identify and actively avoid, including the ones below:
| Patch compliance challenges | Patch compliance strategies |
| Lack of clear patching protocol | Establish a formal patch management policy, assign ownership, and define SLAs for applying updates across devices and applications. |
| Assuming “updated devices are outright compliant” | Align patching practices with frameworks like PCI-DSS, HIPAA, NIST, GDPR, GLBA, and FERPA, ensuring documentation and audit readiness. |
| Legacy systems preventing security updates | Plan phased upgrades or migrations to supported systems, use compensating controls, and budget for lifecycle management. |
| Cost and productivity concerns | Conduct risk assessments to weigh costs against potential security breaches, and use automation tools to reduce downtime and manual effort. |
One proven way to mitigate many of these challenges is by implementing automated patch deployment strategies, usually through an RMM. Internal teams can also ease the burden by setting risk-based prioritization and tracking patching metrics to maintain accountability.
Want to dive deeper into specific patching questions? Check out our Patch Management FAQ for practical answers and expert tips.
How IT teams can maintain patch compliance
Some organizations may forgo system software upgrades or have them delayed to meet business objectives. Others simply lack a common understanding of how software upgrades impact workflows. But IT teams and MSPS can be a bit more proactive by adopting some of these timely practices:
System software upgrades
There can be several reasons why organizations delay or skip software upgrades, as well as security patches. From a lack of resources to being concerned about the impact of software upgrades on business operations.
However, compared to the damage caused by data infringement or ransomware attacks, these reasons appear as a minor inconvenience.
Software that is not updated in a timely fashion becomes susceptible to many vulnerabilities and will eventually become a target for cyberattacks.
On top of that, continued use of unsupported software compromises the overall patch compliance, which likely leads to failed compliance with regulations like GDPR, HIPAA, and PCI. As a general rule, all software and third-party applications must be updated regularly to maintain compliance.
Organizations struggling to monitor the health and security levels of their endpoints can use IT management software to help with patch management and visibility.
System health
Patches are often released with an associated severity level ranging from Low to Critical. While this is sometimes used to triage patching operations by priority, it’s also a means to qualify overall system health status. The number of patches needed in varying severity levels helps to determine this rating:
Healthy Systems have all updates and current patches installed. Vulnerable Systems have missing patches of low or moderate severity levels. Highly Vulnerable Systems are missing patches of critical severity levels and can be considered in immediate danger from cyberattacks, zero-day exploits, and other vulnerabilities.
This system of categorizing system health can be used to create a patch policy and standards for gauging the overall health of the IT infrastructure.
Automated patch management
We’ve mentioned automated patch management several times because it eliminates many gaps in IT asset management cycles, including patch management and auditing.
Patch compliance involves many steps, which leaves room for human error or oversights. The power of automation can transform patch management from a manual problem to one handled by scripts and machine learning.
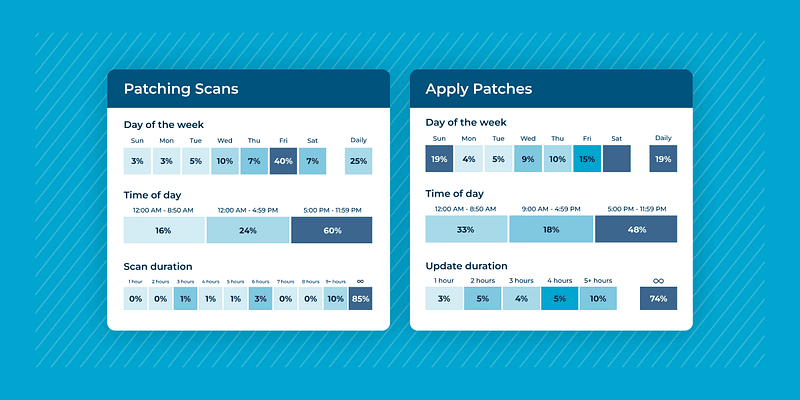
A patch management software like NinjaOne can alleviate the burden on IT teams by scanning systems for missing patches, automating the deployment of updates, allocating the correct patches to the systems that need them, and ensuring that patches do not create compatibility issues.
Delegating all of this work to automated patch management strengthens the cycle of maintaining patch compliance and removes much of the associated risk.
Implement a Phased Testing and Deployment Strategy
Even with automated deployment, never apply patches directly to your entire production environment. A mature strategy involves a phased approach: first, deploy the patch to a small group of non-critical “canary” or test devices. After a successful soak period (e.g., 24-48 hours) with no reported issues, roll it out to a larger pilot group, and finally, deploy to the remaining production environment. This process drastically reduces the risk of an update breaking a critical business application while still ensuring timely compliance.
Endpoint visibility with compliance reports
As we mentioned earlier, patching is only part of the compliance question.
Organizations still need visibility into all of their devices to ensure that no assets are left unchecked. A lack of endpoint visibility and inventory can hamper the process of making all devices compliant, so an accurate inventory is essential.
Once this inventory is created, an automated patch management tool can be deployed to help make informed decisions about patch compliance. The best patch management tools automatically generate patch reports that illustrate compliance across all devices in the IT environment by monitoring each device’s patch status.
These reports are your key to audit readiness. Auditors specifically look for two things: 1) Evidence of a formal policy that defines remediation timelines, and 2) Historical proof that the policy was followed—meaning, documentation showing when a vulnerability was detected, when the patch was applied, and a final log confirming successful deployment within the time frame set by your policy (e.g., 30 days).
Patch management software for patch compliance
In larger enterprise applications, the IT staff typically sets up automated updates to be carried out across many systems without requiring human intervention. This frees up considerable IT resources while still keeping the organization compliant.
When it comes to larger use cases, it’s nearly impossible to keep up with software updates without the help of patch management software tools.
NinjaOne is a complete patch management solution that makes it easy to automatically patch all your Windows, Mac, and Linux endpoints from a single console. With our solution, IT teams and MSPs can achieve cross-platform visibility on all managed endpoints and the automation tools required to keep them secure and compliant.