Key Points
- Dynamic Lifecycle Governance: Data security management provides ongoing oversight of information across cloud and endpoint infrastructures.
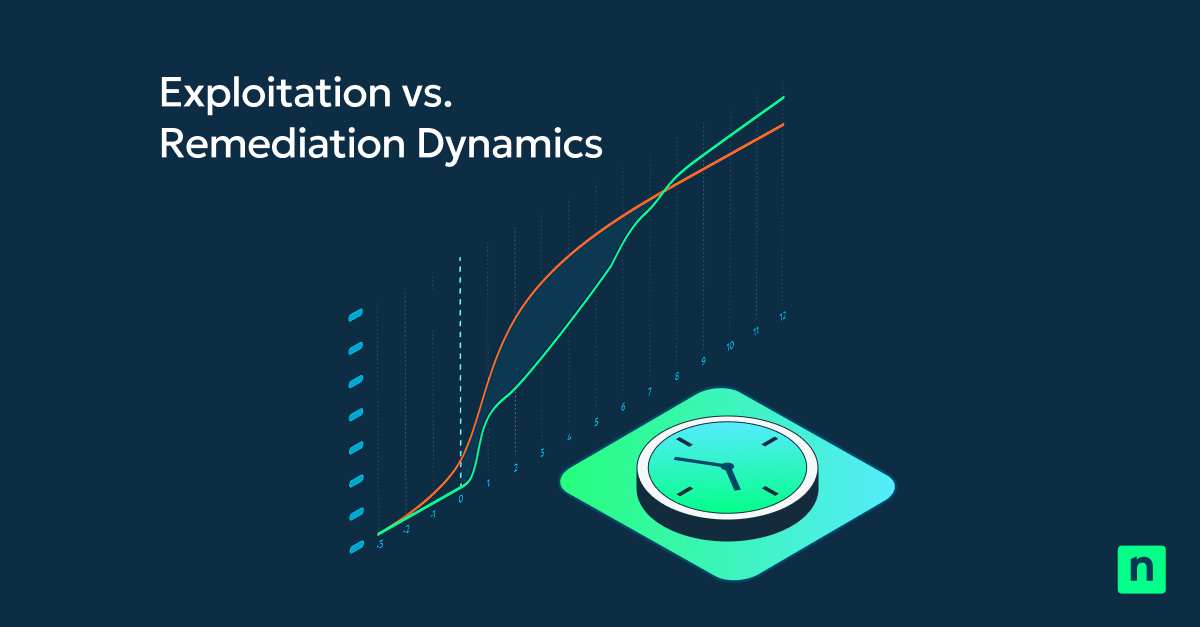
- Proactive Risk Mitigation: Shifting from static checklists to real-time assessments allows organizations to counter emerging zero-day threats.
- Structured Data Ownership: Defining clear roles for Data Owners and Custodians ensures accountability for classification and encryption.
- Automated Visibility and Control: Leveraging automated discovery and RBAC prevents data sprawl and unauthorized access.
- Integrated Policy Monitoring: Constant surveillance for policy drift ensures technical controls remain effective against configuration decay.
Data security management (DSM) is the practice of tracking how information is protected, accessed, stored, transferred, and deleted across endpoints over time for optimal data safety. This ongoing measure helps safeguard sensitive information, but it’s hard to know where to start, especially if you process vast amounts of data.
Data security governance reduces uncertainty
Having a proactive approach to how your information is processed helps you evolve alongside external threats, underscoring the need for remote monitoring tools.
What data security management encompasses
Data security management helps stakeholders gain control over how consumer data moves across your infrastructure for sustained protection. Here are the roles DSM plays in your organization:
- Marking sensitive data: Automates the search for PII (Personally Identifiable Information), PHI (Protected Health Information), and IP (Intellectual Property)
- Establishing access/usage: Maps out Role-Based Access Control (RBAC) for read, write, and delete rights
- Implementing security controls: Applies full-disk encryption (FDE) when data is stored; Transport Layer Security (TLS) during data transfers
- Detecting policy drift: Uses Security Information and Event Management (SIEM) to monitor and catch security outliers.
How data security management differs from checklists
Security checklists, like those used in regular/continuing PCI-DSS audits, only show one facet of how data is safeguarded. Enforcing data security management practices grants a continuous “feed” of your IT environment’s resiliency.
- Static checklists can tell you whether a firewall is on, while DSM can provide insights into firewall rules after cloud services create containers for uploaded data.
- Data security management practices assign Data Custodians in charge of encryption, and Data Owners for classification purposes.
- DSM involves Continuous Risk Assessment, which is triggered when new threats arise (such as a new zero-day exploit).
| Feature | Security checklists | Data Security Management |
| Operations | Confirms a point-in-time state of your security posture | Adapts to real-time changes (e.g., firewall state post-cloud bucket spin up |
| Adaptability | Rigid annual or bi-annual review process | Real-time risk assessments based on new threats |
| Accountability | Typically delegated to IT teams | Distinguishes IT roles and business unit responsibilities |
| Focus | Aimed at passing audit metrics and regulatory needs | Helps reduce risk via consistent policy enforcement |
| Growth | Only addresses new systems in succeeding reviews | Scales automatically as data movement and volume increase. |
Core pillars of effective data security management
Visibility
Being aware of where your data is, along with what it represents, is the first pillar of data security management. You can’t protect what you don’t see. So unified endpoint monitoring platforms (e.g., NinjaOne) specialize in automating detection for around-the-clock security.
Access control
Enforcing least privilege, assigning ownership, and detecting permission drift are vital steps to securing business-critical assets. Ensure users only have the minimum level of access required for their roles.
Protection
Becoming resilient against outside attacks means adding protective layers around your data. AES-256 encryption and tokenization practices help shield important databases that store sensitive information, like health records or payment information.
Monitoring
Tracking user behavior on an endpoint helps you define unusual activity and possible breaches. If your endpoint manager can flag suspicious activity, such as a 40GB company data download on a Saturday night, you’ll have more ways of detecting compromised systems.
Governance
Data security management also involves the legal and policy framework that holds everything together. Maintain an Incident Response Plan (IRP) for full preparedness, and a Data Retention Policy (DRP) to guide data retention for reduced liabilities.
Aligning data security with business and compliance needs
Your enterprise should be able to enjoy full functionality with implemented safety rails. Achieve operational efficiency with:
- Concise categorization levels
- Regulation compliance
- Security-usability balance
Operational challenges in data security management
Data sprawl
Modern IT infrastructures rely on cloud-based services for some of their most essential platforms. This dependence on Software-as-a-Service (SaaS) has redefined operational spending completely. But it also introduces certain downsides.
Having one too many SaaS in your company’s toolbox can create a sprawl of data, making it harder to keep track of ownership, least-privilege, and more. Keep this in mind, and employ centralized solutions to keep IT management simple.
🥷🏻| Unify IT management tools for easier visibility.
Read how NinjaOne automates patch deployment and data reports while streamlining disaster prevention.
Shadow IT
Rigid guardrails may cause employees to use outside tools to speed up their workflows. While fast turnaround times are key for operational efficiency, you’ll want to prioritize the safety of your infrastructure first.
Skill gaps
Employees who don’t meet the necessary expertise needed to be cognizant of international/local regulations and technical implementation can produce less than stellar results. Verify helpdesk applicants thoroughly.
Limitations and important considerations
Data security management determines how information is handled across your entire IT infrastructure, but it isn’t a “one-size-fits-all” solution. So understanding its constraints is just as relevant as evaluating its uses.
DSM dictates what must be protected and how, but it isn’t the only part of your security framework. Strategic policies are useful for enterprise-wide safety. But it’s purely documentation without the technical tools you need (e.g., AES-256).
Moreover, data moves through multiple departments (Marketing, Finance, Security), so your data security management plan must account for scale. As your departments grow, so should your IT helpdesk’s budget.
Cloud migration, AI integration, and newer threats (e.g., ransomware-as-a-service) mean that policies written now can be obsolete in six months. As such, leading enterprises can’t afford rigid checkbox policies any longer, highlighting DSM tools that provide more at reduced cost.
💡Important: Beware of these common misconceptions about data security management:
- Organizations don’t need continuous governance
- IT experts are solely responsible for data security
- Compliance equates to total security
Data security management provides ongoing support
Your enterprise data security strategy needs ongoing controls, ownership, and tracking to take on modern threats, meet demands, and prioritize efficiency. And with the right tools, you can simplify IT management with centralized dashboards.
Related topics: