There’s no doubt that the typical modern enterprise generates large amounts of data that must be moved, analyzed, and safely stored. Because much of this data involves the privacy of users and customers, various laws and regulations have been created to drive strong protection practices. While these regulations vary a great deal from country to country, the underlying concept remains the same: keep data safe while making it available to authorized users when they need it.
What this article will cover:
- What is data protection?
- Data protection in the US
- Data protection in Canada
- Data protection in the EU
- The 7 principles of data protection (GDPR)
- Data protection solutions
What is data protection?
Data protection is the concept of safeguarding important data from corruption, compromise, or loss. It doesn’t just involve passive protection, rather it leans heavily on processes for restoring and recovering data should something happen to render the data inaccessible or unusable. Data protection also covers matters of compliance with applicable legal or regulatory requirements.
In addition to security, data protection is concerned with the authorized access to data. Obviously, one can’t simply delete important data or lock it inside an impenetrable vault. Data is meant to be used, and protected data must be available to authorized users when needed for its intended purpose.
In broad terms, the modern idea of data protection spans three broad categories: traditional data protection such as backups; data security and breach defense; and data privacy.
The first principle of data protection
The primary principle of data protection is to engage methodologies and technologies to protect data while making it available to authorized users under all circumstances.
Beyond this basic maxim, data protection becomes very granular depending on the region in question. Various laws and government regulations add layers and details to this broad-level objective, taking into consideration myriad cybersecurity concerns and matters of personal privacy.
As we continue, we’ll explore data protection as defined within different regions.
Data protection principles in the United States
Unlike some regions, notably the European Union, the United States does not have a comprehensive federal law governing privacy and the handling of data or personal information. Instead, organizations in the US must navigate an amalgam of federal and state laws that regulate the collection, processing, disclosure, and security of personal information (PII).
In addition, certain industries such as healthcare and finance are regulated in ways unique to their sector.
Because of the decentralized nature of US data protection laws, data controllers have to stay up to date with these varied laws and prepare for likely further evolution in US data regulation.
Let’s take a quick look at the major data protection laws currently in the books:
HIPAA
The Health Insurance Portability and Accountability Act of 1996 (HIPAA) is a federal law that establishes standards when safeguarding certain health-related personal information from being disclosed without the patient’s consent or knowledge.
The HIPAA Privacy Rule, brought forth by the US Department of Health and Human Services, went into effect in 2003 and regulates the use and disclosure of protected personal information in healthcare treatment, payment, and operations.
An additional HIPAA Security Rule also went into effect in 2003 which deals specifically with electronic medical records. This rule specifies administrative, physical, and technology safeguards required for compliance.
FCRA
The Fair Credit Reporting Act (FCRA) is a federal law governing consumer reporting agencies and their procedures regarding the confidentiality, accuracy, relevancy, and proper use of personal data.
The personal information governed by FCRA is specific to credit reporting and consumer reports sold for purposes of determining eligibility for employment, for credit or insurance underwriting, and for certain other purposes described in the FCRA.
The FCRA also includes several protections for consumers, including the right to obtain one’s own credit score and the right to know what is in the file that a consumer reporting agency maintains on the consumer.
GLBA
The Gramm-Leach-Bliley Act of 2002 (GLBA) is a federal law that primarily regulates the collection, use, disclosure, and protection of nonpublic personal information collected by financial institutions.
COPPA
The Children’s Online Privacy Protection Act (COPPA) is a federal law that imposes requirements on websites directed to children under 13 years of age and on operators of websites or online services that knowingly collect personal information from children under 13 years of age. Operators covered by COPPA must disclose certain information in their privacy policy and obtain parental consent before collecting certain types of information from children under the age of thirteen.
FERPA
The Family Educational Rights and Privacy Act (FERPA) is a federal law that covers the protection of students’ educational records. FERPA applies to any public or private elementary, secondary, or post-secondary school, as well as state or local education agencies that receive funds under certain US Department of Education programs.
FERPA gives parents and eligible students greater control over their educational records, as well as prohibiting educational institutions from disclosing personally identifiable information in education records without written consent from an authorized individual
TCPA
The Telephone Consumer Protection Act (TCPA) is a federal law regulating telemarketing calls, auto-dialed calls, recorded calls and automated text messages, and unsolicited faxes. TCPA also lays out technical requirements for fax machines, autodialers, and voice messaging systems and how to identify users of such equipment.
Privacy act
The Privacy Act of 1974 is a federal law that applies largely to federal government agencies, contractors, and employees. The Privacy Act restricts disclosure of personal information maintained by government agencies and grants individuals increased rights of access to agency records maintained on themselves. This law also establishes a code of fair information practices with statutory requirements for collection, security, and dissemination of personal records.
Data protection principles in Canada
Data protection laws in Canada are similar to those in the US in that they consist of a complex set of federal and provincial statutes. Like within the US, some of these laws enforce regulations on specific sectors. Certain statutes include mandatory notification and reporting requirements in the case of a breach of personal information.
The key data protection statutes in Canada include:
- Federal: Personal Information Protection and Electronic Documents Act 2000 (PIPEDA)
- British Columbia: Personal Information Protection Act (BC PIPA)
- Alberta: Personal Information Protection Act (AB PIPA)
- Quebec: Act Respecting the Protection of Personal Information in the Private Sector (Quebec Private Sector Act)
Canada has also enacted an anti-spam law, Canada’s Anti-Spam Legislation (CASL), which involves electronic marketing activities such as data collection and bulk email sending.
Data protection principles in the European Union
The European Union currently boasts the most comprehensive data protection framework in the world. The General Data Protection Regulation (GDPR) enacted in 2018 serves as the legal framework for data protection and privacy for every member state.
This complex legislation also affects any business conducting trade with the EU and carries stiff fines and penalties to ensure GDPR compliance. The GDPR is designed to protect EU citizens’ sensitive data and give them more control over how it is accessed and used. Requirements include controls over international data transfers and citizens’ rights to have data deleted.
We’ll explore the GDPR in greater detail in the next section.
The 7 principles of data protection (GDPR)
-
Lawfulness, fairness and transparency
GDPR Article 5(1)(a): “Personal data shall be processed lawfully, fairly and in a transparent manner in relation to the data subject (‘lawfulness, fairness, transparency’)”
Specifies that organizations must ensure their data collection methods don’t compromise the law and that their use of data is transparent to those whose data is being collected.
-
Purpose limitation
GDPR Article 5(1)(b): “Personal data shall be collected for specified, explicit and legitimate purposes and not further processed in a manner that is incompatible with those purposes; further processing for archiving purposes in the public interest, scientific or historical research purposes or statistical purposes shall not be considered to be incompatible with the initial purposes”
States that organizations must only gather personal data for a defined and stated purpose. They must outline what the purpose and goal is, and only collect data for the time that they need to achieve these ends.
Data collection and processing that is carried out for historical, scientific, or statistical research, or for reasons in the public interest, is granted more freedom.
-
Data minimization
Article 5(1)(c): “Personal data shall be adequate, relevant and limited to what is necessary in relation to the purposes for which they are processed (data minimization).”
Organizations should only retain the smallest amount of data needed for their requirements. Gathering “extra” data in hopes that it will be useful later is not allowed.
-
Accuracy
Article 5(1)(d): “Personal data shall be accurate and, where necessary, kept up to date; every reasonable step must be taken to ensure that personal data that are inaccurate, having regard to the purposes for which they are processed, are erased or rectified without delay (‘accuracy’)”
Personal data collected should be suitable for the stated purpose as well as accurate and up-to-date. Personally identifiable information must be reviewed regularly, and inaccurate information must be corrected or deleted.
-
Storage limitations
Article 5(1)(e): “Personal data shall be kept in a form which permits identification of data subjects for no longer than is necessary for the purposes for which the personal data are processed; personal data may be stored for longer periods insofar as the personal data will be processed solely for archiving purposes in the public interest, scientific or historical research purposes or statistical purposes subject to implementation of the appropriate technical and organizational measures required by the GDPR in order to safeguard the rights and freedoms of individuals (‘storage limitation’)”
After the objective of collecting data is met, that data should be deleted. If there is an acceptable reason for keeping the information, for example that it can be used for public interest or historical research, the organization must set and justify a retention period.
-
Integrity and confidentiality
Article 5(1)(f): “Personal data shall be processed in a manner that ensures appropriate security of the personal data, including protection against unauthorized or unlawful processing and against accidental loss, destruction, or damage, using appropriate technical or organizational measures (‘integrity and confidentiality’).”
Any information retained must be kept securely. Your organization should make sure that adequate data protection measures are set to safeguard personal information. A commitment to cybersecurity is essential.
-
Accountability
Article 5(2): “The controller shall be responsible for, and be able to demonstrate compliance with [the other data protection principles]”
This means that organizations should take responsibility for the data they retain and show compliance with all the other principles. Organizations should be able to document and prove their adherence to these practices.
This may involve:
Keeping up to date on data protection practices
Creating a Data Protection Officer (DPO) or compliance officer position
Establishing a personal data inventory
Performing data protection impact assessments and cybersecurity audits
NinjaOne and data protection
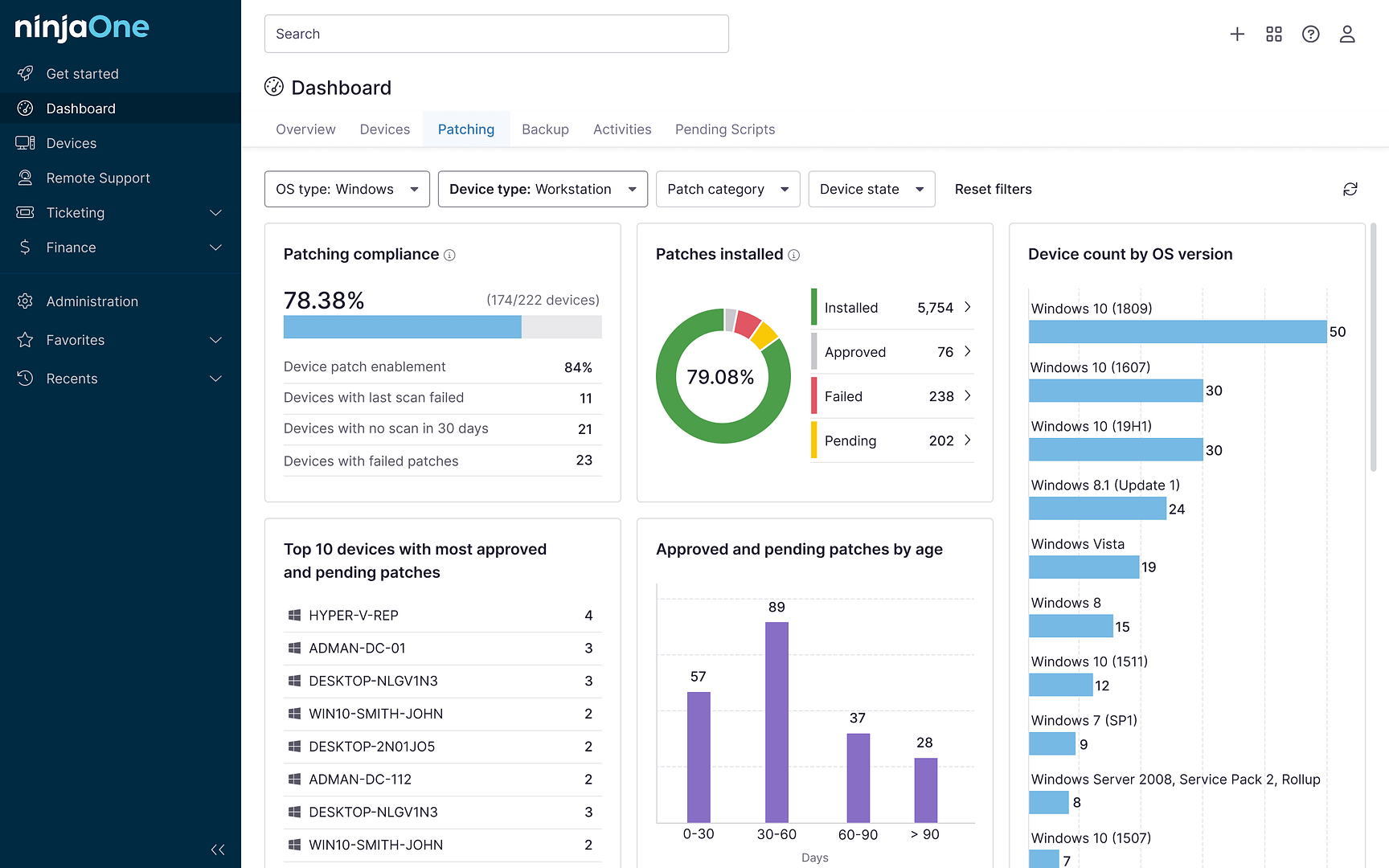
Features like Ninja Data Protection are designed to help organizations and IT providers tackle the complexities of data protection regulations.
- Full Image Backup
- Document, File, and Folder Backup
- Endpoint Management
- Patch Management
- Bitdefender Advanced Threat Security
- Comprehensive Ransomware Defense
Conclusion
Data protection is the process of securing information against compromise or corruption. It may be a challenge for many organizations, but it is essential in the modern world of high-value data and increasing cyberthreats.
Both end users and IT providers need to ensure that strict security measures are in place and compliance is maintained in regions or industries where it’s required — and choosing the right solutions and partners can be lifesaving when it comes to navigating the complex waters of data protection.