Looking for the best remote access software? Nowadays, businesses have shifted to hybrid and remote setups where employees work in offsite locations. Because of this, the need for secure remote access, remote support, and device management has never been greater.
It can be difficult to securely access and control all your organization’s endpoints, but secure remote access solutions simplify and streamline that process. In this upcoming blog, we’ll explain more about remote access and what it can offer your business.
Table of Contents
What is secure remote access software?
Remote access solutions consist of tools and software that provide access to computers and devices anywhere. This helps organizations to easily enable authorized access to devices so that remote support and management can be executed. Remote access software is the key to establishing secure remote control of offsite devices.
What to consider when choosing the right remote access software?
Determining which remote access solution to choose and incorporate into your IT environment can be challenging. Here are some major elements to factor into your decision:
Ease of use
Remote access should be quick so that there’s less time spent trying to access the endpoint and more time supporting and maintaining your computers. NinjaOne offers a remote access solution that makes it easy for you to take control of your organization’s endpoints.
Integrates with existing IT environment
Implementing remote access software that integrates well with your existing tools allows IT teams to deploy the software faster. It makes using it more efficient alongside other functions such as help desk software or remote monitoring. Trying to incorporate new software that doesn’t integrate with your current software can cause downtime or disrupt IT operational workflows.
Reliability
A well-performing remote access solution is dependable and efficient. Choose remote access software that you can rely on to access and manage devices wherever they’re located quickly. Unstable connections block progress and can cause frustration, impacting end-user satisfaction and productivity.
Scalability
As your business grows, so does your IT environment. The best remote access software for your business is flexible enough to accommodate changes in your business needs. Scalable software also lowers costs since it removes the need to switch to a different platform with more powerful capabilities.
Excellent quality of support
When choosing a remote access software provider, opt for one that’s proven to provide excellent customer service. Being able to talk to friendly and knowledgeable support personnel makes it easy to resolve any issues. World-class support responds quickly to tickets, making it easy and convenient when you’re looking for answers to questions or solutions for issues.
Best secure remote access software solutions
1. NinjaOne
NinjaOne simplifies IT operations for IT and MSP teams with a unified IT management platform that simplifies IT operations with a comprehensive suite of tools. As an industry leader, NinjaOne stands out for its ease of use and #1 ranked customer support.
As a remote access software, NinjaOne offers a fast connection to endpoint devices and secure and stable control of devices, regardless of where they are located. With built-in remote access capabilities, technicians can swiftly connect to end-users’ devices to troubleshoot issues without disruption or downtime.
In addition, NinjaOne offers seamless integrations with leading third-party remote control tools to give users a wide breadth of choices for remote access.
Strengths of NinjaOne:
- User-friendly interface: NinjaOne stands out for its intuitive user interface, which consolidates various IT management tools into one console. Its simple design makes it easy for users to navigate the platform and efficiently manage their IT assets without extensive training.
- Comprehensive endpoint management: NinjaOne supports remote access for various operating systems, including Windows, macOS, and Linux. This versatility ensures that IT teams can manage and support a wide range of devices within their organization from a single console.
- IT automation: NinjaOne’s powerful automation capabilities enable IT teams to automate routine tasks such as updating software or systems and alerts. This reduces manual interventions and frees up IT teams to focus on strategic tasks.
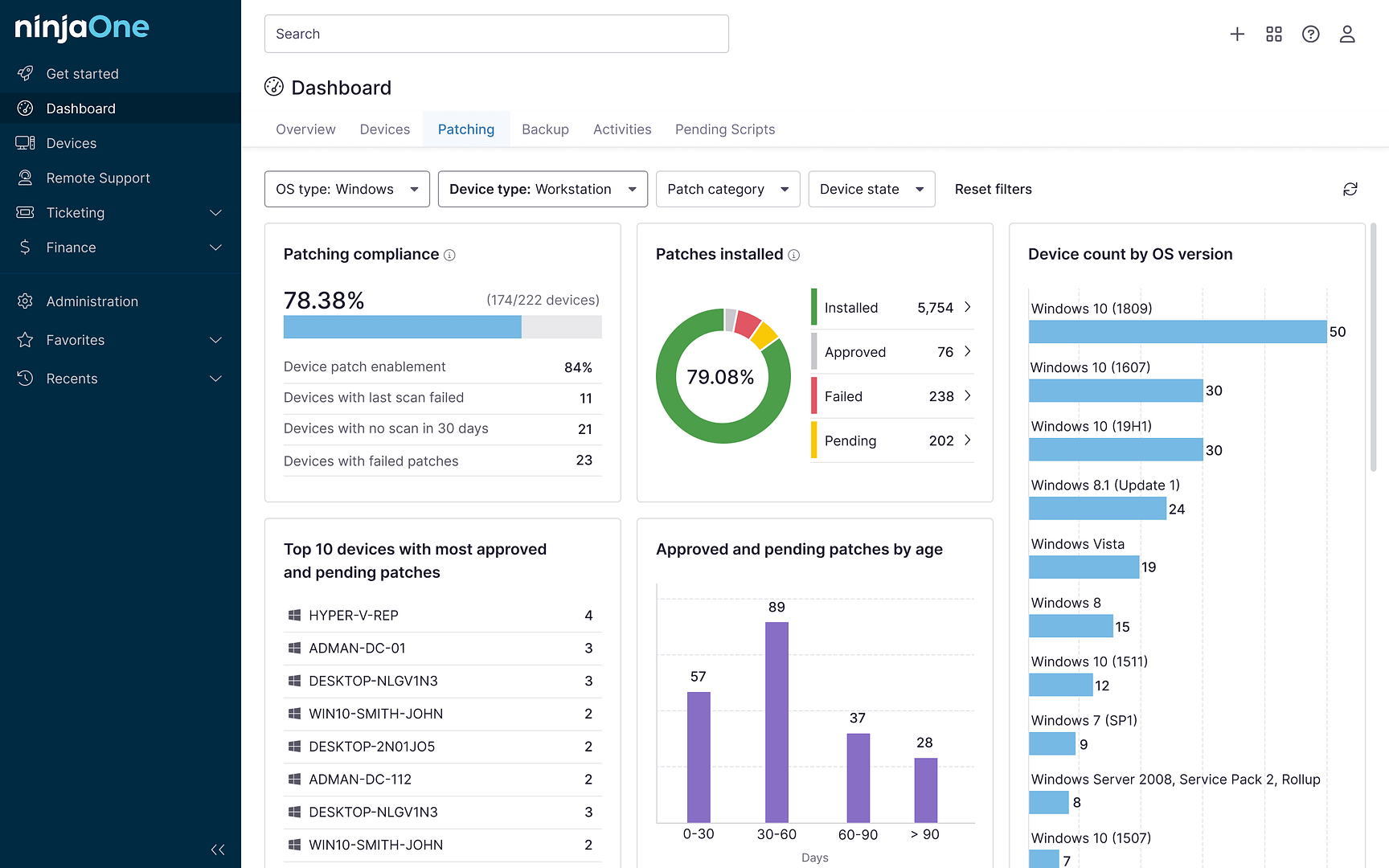
- Patch management: NinjaOne’s automated patch management ensures that all systems are up-to-date with the latest software updates. This reduces the risk of vulnerabilities and ensures high performance of devices.
- Mobile device management (MDM): NinjaOne enables IT teams to manage company-owned and BYOD Android and Apple endpoints to keep these mobile devices secure and provide an accurate, real-time inventory of these devices.
Ninja’s remote access tools give you secure one-click access to your managed endpoints for fast and effective remote support.
2. Anydesk
AnyDesk is a cloud-native remote access software that allows users to connect with and control devices from any location. This solution allows technicians to access files and troubleshoot any issues.
Benefits:
- Cross-platform compatibility: Anydesk is compatible with Windows, Mac, Linux systems and also Apple and Android mobile devices.
- Integrates with third-party apps: Third-party applications can be integrated with the Anydesk platform, giving IT teams more flexibility.
- Automation: Anydesk allows users to configure automations to execute routine tasks without the need for manual intervention from technicians.
Drawbacks:
- Slow performance: Reviews say that the software can be slow and some users reported lag when connecting to remote workstations.
- Complex configuration: Users have said that Anydesk requires complicated configurations to customize the software fully to their needs
- Unintuitive interface: Anydesk’s interface makes it challenging to navigate. Reviewers have said that some fields and features are difficult to locate.
3. RemotePC
RemotePC offers a secure solution for remote access, allowing users to connect to endpoint devices from anywhere. It supports various platforms, including Windows, Mac, Linux, iOS, and Android, ensuring connectivity across endpoint devices.
Benefits:
- Cross-platform compatibility: RemotePC can connect with any endpoint device, making it a flexible and comprehensive choice.
- Simple interface: According to reviews, RemotePC’s interface is simple and easy to understand.
- Easy setup: Users find that RemotePC does not require a lot of time to implement initially.
Drawbacks:
- Slow performance: According to users, the platform can slow down when accessing applications on the remote computer.
- Remote connectivity issues: RemotePC’s remote control connection has difficulty connecting to macOS devices.
- Screen resolution problems: When connecting remotely, users find that the resolution becomes very small and can be difficult to adjust.
4. Getscreen.me
Getscreen.me is a remote access software that offers instant connection to any remote device from a cloud-based web browser application. It offers features like file transfer and session recording.
Benefits:
- Cross-platform support: Getscreen.me allows users to connect to Windows, Mac, and Linux workstations, as well as Android and Apple mobile devices.
- Simple interface: Reviews state that Getscreen.me’s interface is easy to navigate and learn.
- Third-party integrations: Getscreen.me can easily integrate with an organization’s existing IT management software.
Drawbacks:
- Slow performance: Users find this solution’s remote connectivity slow.
- Limited sessions: Getscreen.me has set limits for the amount of remote sessions per day. This limit is determined by the users’ subscription.
- No mobile app: According to reviews, the Getscreen.me platform cannot be accessed on Apple or Android mobile devices yet.
Support end-users and troubleshoot issues from anywhere with NinjaOne’s Remote Access Solution.
5. RealVNC
RealVNC is a remote access software that allows users to remotely control endpoint devices from another computer or mobile device. This solution provides a secure and reliable way to troubleshoot, access files, and manage devices.
Benefits:
- Seamless integrations: RealVNC allows for smooth integrations with third-party applications, giving IT teams more flexibility.
- Scalability: As a business grows, RealVNC can adapt to changing needs and increasing demand for remote access and support.
- Mobile device support: RealVNC allows users to access Android and Apple mobile devices remotely and can integrate with businesses’ MDM solutions.
Drawbacks:
- Login issues: Reviews state that RealVNC’s login portal is complex, so accessing the platform can take a while.
- File transfer: RealVNC’s file transfer feature can be difficult to use, according to some users.
- Complex interface: Users say that the interface needs improvement. Some configurations are difficult and require technical expertise or training to execute.
6. EV Reach
EV Reach is a remote access software that allows technicians to connect to remote endpoints and remotely control these devices. This platform allows IT professionals to troubleshoot and support a distributed workforce efficiently and securely.
Benefits:
- Automation: EV Reach allows users to automate routine tasks to reduce manual workloads and free up IT professionals to work on other tasks.
- Monitoring and reporting: By generating comprehensive reports, users can gain visibility into their IT environment and monitor device performance and health.
- Software management: EV Reach can remotely deploy software or push out software updates.
Drawbacks:
- Setup: According to EV Reach reviews, the onboarding process is not thorough enough so the learning curve can be steep.
- Complex interface: Users find navigating EV Reach’s platform difficult, which can impact IT efficiency.
- Linux support: EV Reach does not work with Linux devices, limiting its remote access capabilities.
Use cases for secure remote access solutions
Remote access software enables employees to work more flexibly and efficiently, regardless of location. IT support teams utilize remote access solutions to provide a secure and reliable means of accessing remote workstations and servers, allowing them to resolve problems at any time. Here are some key use cases for remote access solutions that highlight the value and versatility they provide to any business.
Managing remote workforces
One of the most common use cases for remote access is by IT teams and MSPs to monitor and manage devices of employees who work from home or any location outside the traditional office environment.
Remote access tools enable IT support teams to connect to remote devices and access files and applications without having to spend on travel time to go to the device’s physical location. Remote access software offers flexibility, enabling remote collaboration and reducing travel costs.
IT support
Remote access tools are invaluable for IT support teams, allowing them to remotely troubleshoot and resolve issues on employees’ computers, servers, or network devices. This capability significantly reduces downtime and eliminates the need for physical presence, making IT support more responsive and efficient.
Disaster recovery and business continuity
In the event of a disaster or unexpected disruption, such as a natural disaster or a pandemic, remote access solutions are critical for business continuity. They allow employees to continue working from safe locations, ensuring that business operations can proceed with minimal interruption.
Best practices for implementing remote access tools
To ensure that remote access is efficient and secure, these best practices can help you implement remote access software solutions without any problems:
1. Choose a reputable provider
There are many options on the market for remote access software so analyzing the strengths and features of the top remote access vendors will ensure smooth implementation. G2 awardees, such as NinjaOne, have been voted by IT professionals as the best remote access software solutions on the market.
2. Keep systems and software up-to-date
Regularly updating operating systems, applications, and remote access tools is essential to protect against vulnerabilities. Cyber attackers often exploit known vulnerabilities in software; thus, keeping everything updated minimizes the risks. Patch management goes a long way to keeping your remote access tools secure.
3. Use session logging
Maintaining logs of remote access sessions, including user identities, activity, IP addresses, and timestamps, allows for auditing and monitoring unusual access patterns. This practice helps identify potential security breaches early.
4. Integrate with a comprehensive endpoint management platform
Endpoint management integrations consolidate all the tools that IT support teams need to access devices and resolve issues remotely. This makes it easier and faster for technicians to do their work.
Get started with NinjaOne’s secure remote access software
As remote work steadily increases, it’s essential to have the right tools to control your organization’s computer system. A secure remote access solution enables you to quickly resolve any device or network issues, manage devices, and support continual business operations. To make the most of remote access, read about our suggested remote access best practices.
NinjaOne provides one-click remote control software to give you quick remote access to your endpoints, making it easy and simple to manage your organization’s devices. Sign up for a free trial today.