Ninja’s feature-packed 5.3.1 release provides a ton of out-of-box functionality, better reporting, and improved user permissions. 5.3.1 also includes major updates to Ninja Ticketing that you can read about here.
New monitoring templates
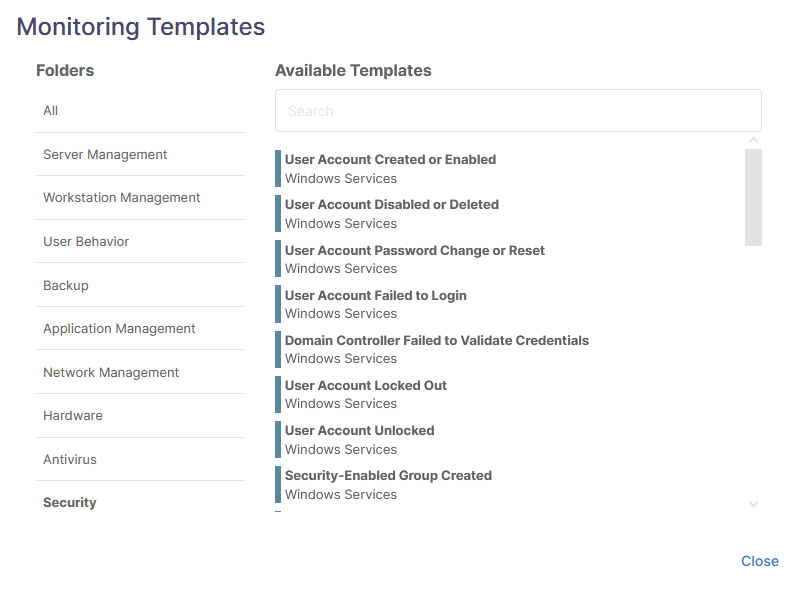
Ninja has always offered a robust set of condition monitoring templates, and in 5.3.1 we’ve redesigned the UI and added a ton of new templates to make monitoring critical information on endpoints and servers easier for our partners.
Monitoring templates
Monitoring templates are pre-configured policy conditions that allow you to monitor specific system states and trigger alerts, tickets, or automations. In our most recent release, we’ve added over 120 additional monitoring templates including:
- Popular backup vendors like Veeam, Acronis, Altaro, and StorageCraft
- Common security solutions, including Sophos, ESET, Windows Defender, and more
- Common server applications and services including Exchange, SQL, WSUS, and more
- VMWare and Hyper-V hosts
- Windows security-related events including user-, log-, and fire-wall related events
We’ve also redesigned the monitoring template interface in the policy management screen, making it easier to find and use monitoring templates.
These new templates are just the first round of new built-in conditions. With our renewed focus on out-of-the-box capabilities, we’re helping our partners shorten their time-to-value and use Ninja’s monitoring capabilities more effectively.
New user permissions model (beta)
Granular and robust user permissions play a critical role in effective security and operational maturity. While Ninja has always allowed administrators to restrict access to appropriate organizations and certain features for individual users, the functionality hasn’t been granular enough or scalable enough, until now.
Ninja’s new user permissions model allows administrators to assign a very granular set of permissions to a role. Each user is then assigned a role or roles to determine which organizations, features, and functionalities they have access to.
Roles can permit or restrict access to:
- Administrative tasks and configurations
- Entire organizations
- Devices data by roles and field type
- Devices actions (like creating a new device, or launching a remote session)
- Policy management globally or for individual policies
- Script management
- Ticketing and ticket management
- Documentation and document management
Permission can generally be set to:
- No Access
- View
- View and update
- View, update, and create
- View, update, create, and delete
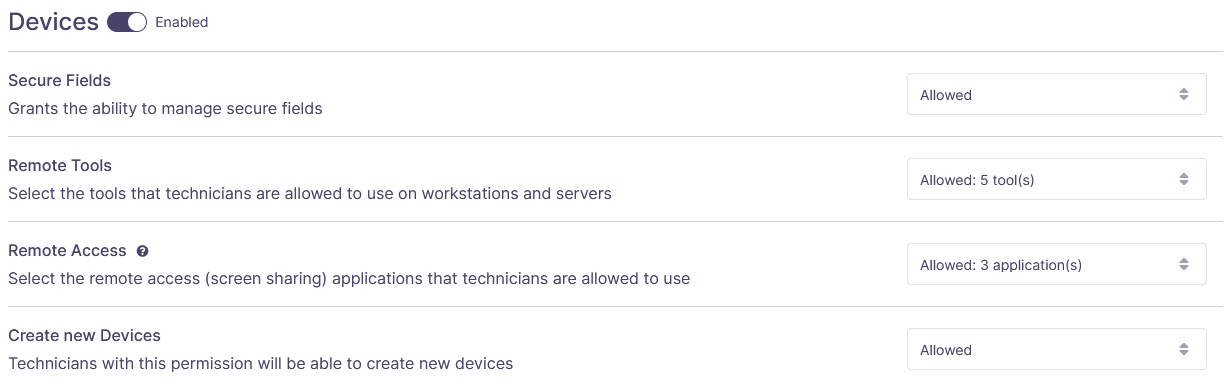
The incredible granularity our new user permission model gives our partners ensures your technicians have the access you need them to have, while the role-based system ensures that permissions can be managed at scale.
Updated report visuals
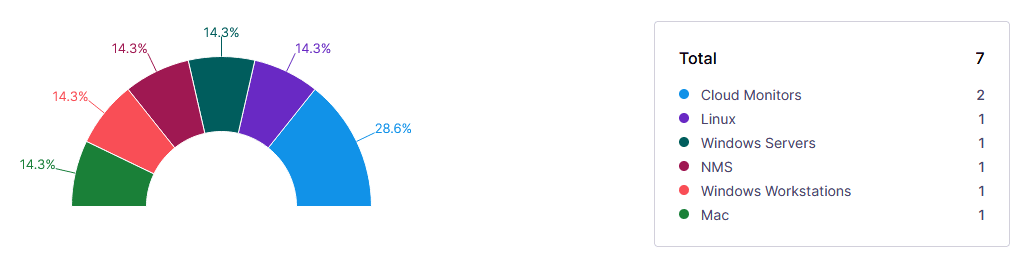
We felt our reports were looking a little on the old side, so we’ve decided to redesign them. The new report designs look much more modern, standardized, and presentation-ready while presenting data in a more easily consumed format.
This is the first step in our plan to improve Ninja’s reporting capabilities with a drag-and-drop editor and more actionable reports coming soon.
Security enhancements
5.3.1 included several security-related enhancements, primarily around user logins:
- Users can now log into Ninja via Windows Hello, Mac Touch ID, and other hardware-based login solutions via WebAuthn protocol
- We’ve released our SAML / SSO integration capabilities to general availability
- Passwords requirements have increased for all new users
See these new updates for yourself
Book a demo or join us at partner office hours to see these changes in action.