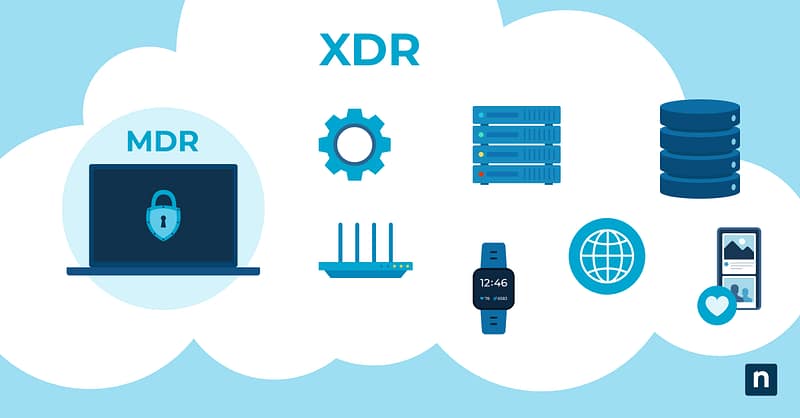
If your IT team is struggling to accomplish its lengthy to-do list, implementing detection and response solutions may be one step you can take to improve efficiency and reduce workload. Endpoint security solutions like Managed Detection Response (MDR) and Extended Detection and Response (XDR) can help you maintain and monitor your endpoints and other parts of your infrastructure, a very necessary capability in modern cybersecurity.
However, the solution you implement will depend on your needs and current infrastructure. Some organizations benefit from MDR while others are better served by XDR. This guide on MDR vs XDR will help you pinpoint the best solution for your organization.
What is Managed Detection and Response (MDR)?
Managed Detection and Response (MDR) is a cybersecurity service that identifies and addresses threats to your organization and security environment. Although the two are similar, it’s important to note that MDR is not the same as EDR. Typically, MDR contains both an automated technological component and a security team component, which allows organizations access to network and environment monitoring as well as research and expert analysis following an incident.
MDR allows organizations to have access to these resources at a fraction of what it would cost them to have in-house. This helps you protect your network, endpoints, and data. To learn more about MDR, watch this short video explaining Managed Detection and Response (MDR).
MDR solutions have a few key capabilities that make them attractive security solutions.
- High visibility: Constant, automated monitoring means that your MDR solution can help you prioritize alerts, identify unusual events or potential threats, and notify you for urgent issues. When you know about an incident early, you can limit the effects and more easily control the damage.
- Incident response and analysis: Because of an MDR solution’s high visibility, they can quickly investigate any threats and determine how to respond effectively. MDR also generally includes expert analysis from your provider. MDR analysis will also prioritize the detected vulnerabilities for you, saving you the time needed to classify and prioritize fixes for those vulnerabilities.
- Filling the skill gap: Many organizations find it challenging to recruit and retain security personnel. Utilizing an MDR solution can help mitigate this issue because it allows you to outsource threat analysis and helps with prioritization. Rather than expending your energy and limited resources on building and training a specialized security team, you can use MDR to handle more challenging threats.
What is Extended Detection and Response (XDR)?
XDR, or Extended Detection and Response, collects data from a wide variety of sources, whether local or cloud-based, to monitor and assess your organization’s security. Using baseline data about your environment, XDR can monitor activities and data access throughout your environment and alert you when there is unusual or suspicious activity.
Although it is similar to MDR, XDR collects data from a wider variety of sources across a network and is designed to provide a complete view of potential security vulnerabilities. Key features and capabilities of XDR solutions include:
- Advanced machine learning: While MDR also uses machine learning, XDR has a leg up due to its much larger data pool. Because XDR collects data from a larger number and variety of sources, a more holistic picture is created. Artificial intelligence analyzes the data pulled in from your environment and can help detect and respond to complex, advanced (and very sneaky) threats.
- Broad scope: Because XDR solutions pull information from so many places, they are very good at quickly identifying attacks that target multiple components of your environment. Some threats that would normally escape notice or hide from more traditional detection strategies can be caught by XDR software.
- Alert consolidation: One of the major issues faced by security teams is alert fatigue, and XDR can help reduce that. By combining its wide scope with machine learning, XDR solutions analyze every alert generated and determine which are significant or urgent threats that need to be handled by security teams. Instead of receiving alerts for every potential vulnerability, your team only sees alerts for those that meet certain benchmarks.
Endpoint security strategy: MDR vs XDR
There are several factors to consider when selecting an endpoint security solution.
- Real-time threat detection and response capabilities: Both MDR and XDR offer this, but you will want to consider whether your team can handle responding to alerts or not. If not, an MDR solution may work better for your organization. Regardless, real-time threat detection and continuous monitoring are useful and important tools for strong security.
- Overall cybersecurity strategy: Threat hunting, alerting, and response capabilities are all essential for your overall cybersecurity strategy. That in mind, to determine whether MDR or XDR is best for you, consider how your resources are currently used and whether you need more time or more expert input.
- Budget constraints: Be sure to weigh the cost of hiring security experts internally against the cost of managed solutions. Also, account for the cost of basic endpoint security, and then determine whether it is worth the additional cost to your organization to also be monitoring the network and other potential attack vectors. Above all, remember that the cost of a breach will almost certainly be more than the cost of preventative measures.
Improve your security posture with the right response framework. Watch MDR vs XDR: What’s the Difference? today.
Choosing the right endpoint security solution
Ultimately, whether you choose MDR or XDR (or a combination of both) depends on whether you need a security team or a way to improve efficiency for the team you have. MDR solutions can be combined with XDR software, so you could easily retain an MDR provider that uses XDR to manage your environment. However, if you do not feel that you need the outsourced security team and you want advanced cybersecurity, XDR may be the better choice for your organization.
The automated monitoring and alerts, machine learning, and high visibility of these solutions will contribute to early threat detection, enabling your organization to react to threats and attacks before they become a hindrance. Whether you choose MDR or XDR, however, improving your approach to cybersecurity will serve you well.