NinjaOne Critical Patch Prioritization for Smarter Endpoint Security
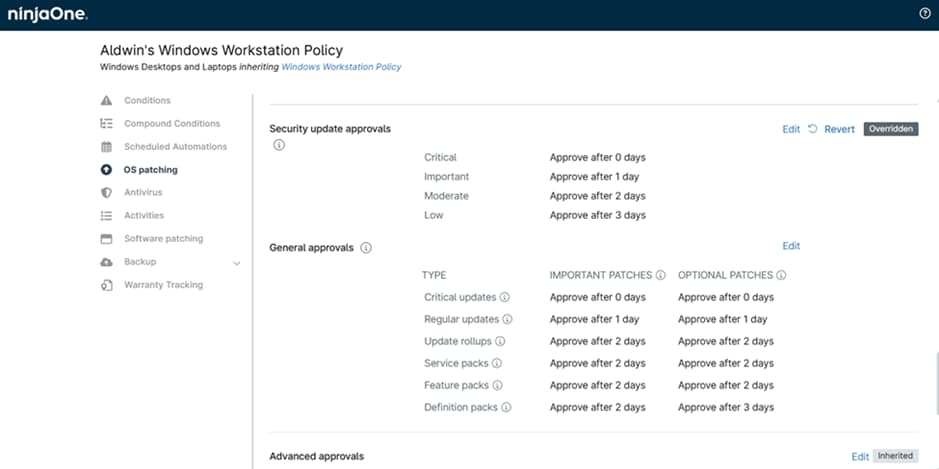
NinjaOne’s critical patch prioritization gives IT teams the severity context, AI-driven insights, and policy-based automation to identify and act on the most dangerous vulnerabilities first. Stop treating every patch the same and start remediating what matters most, faster.