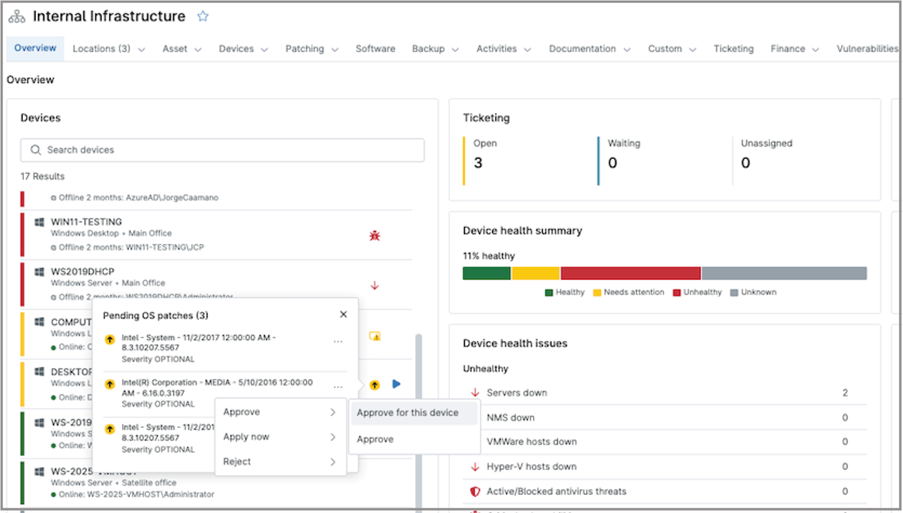
Not every endpoint should be patched the same way, gain precise control where it matters most
Gain granular patch management and flexible control at the endpoint level, giving IT teams the precision to handle exceptions without disrupting broader policies.