KB5078766: Overview with user sentiment and feedback
Last Updated April 28, 2026
Probability of successful installation and continued operation of the machine
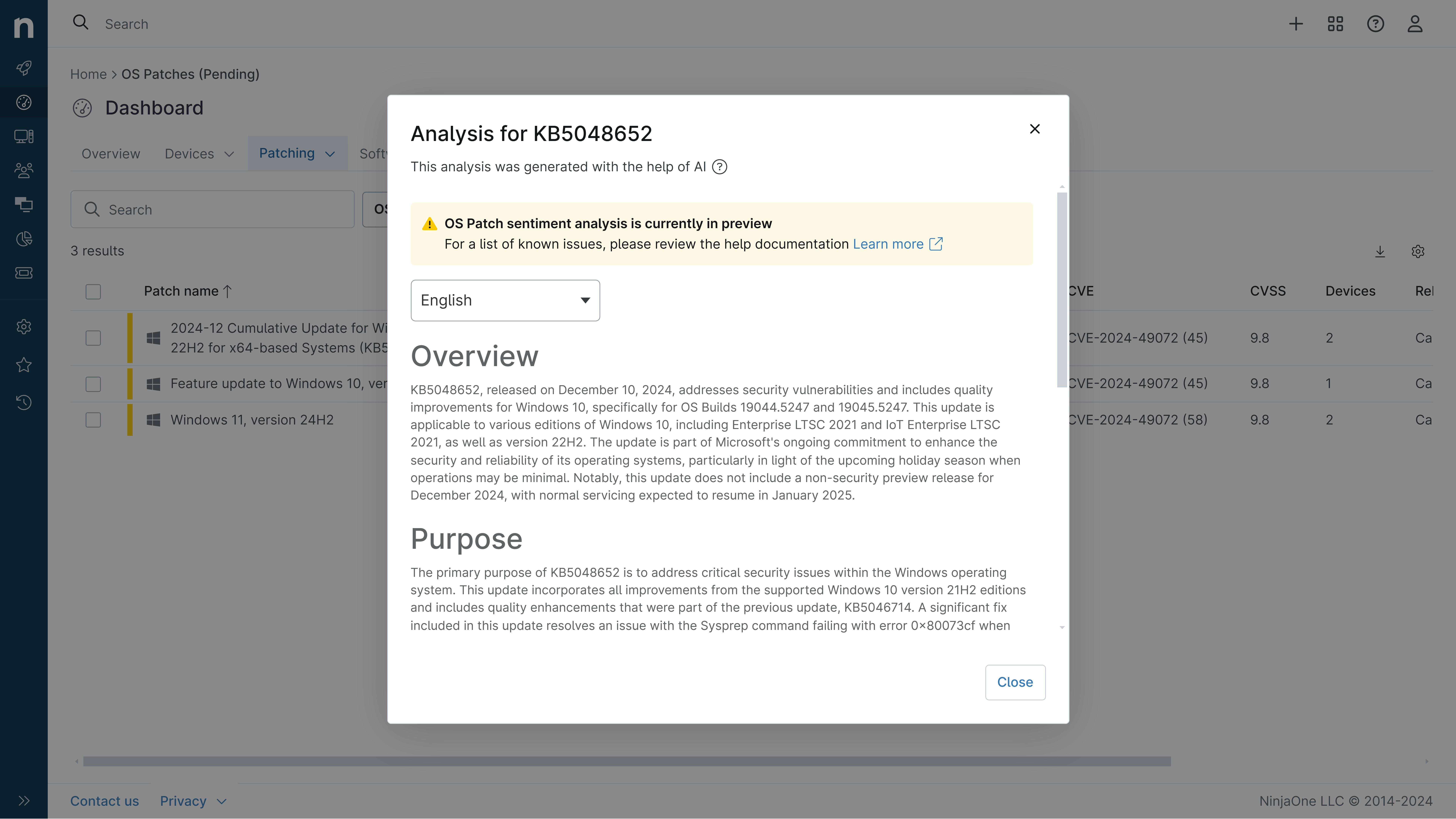
Overview
KB5078766 is a cumulative security update for Windows Server 2022, released on March 10, 2026, with OS Build 20348.4893. This update represents a monthly rollup that consolidates security fixes and quality improvements from previous releases, specifically incorporating enhancements from KB5075906 (February 10, 2026) and KB5082314 (March 2, 2026). The update is distributed through multiple channels including Windows Update, Windows Update for Business, and Windows Server Update Services (WSUS), ensuring broad accessibility for enterprise and standalone deployments.
This cumulative update includes both security vulnerabilities addressed and non-security quality enhancements. Notably, the update is combined with servicing stack update KB5078763 (version 20348.4880), which improves the underlying infrastructure responsible for installing Windows updates. The combined package approach ensures that systems receive both the foundational servicing improvements and the latest security patches in a single installation, streamlining the update process for Windows Server 2022 administrators.
General Purpose
This update delivers critical security fixes and quality improvements essential for maintaining Windows Server 2022 system integrity and reliability. The primary focus areas include enhanced Secure Boot certificate management and improved Windows System Image Manager functionality. The Secure Boot improvements expand device targeting capabilities through additional high-confidence diagnostic data, enabling more devices to automatically receive updated Secure Boot certificates through a controlled, phased rollout mechanism. This is particularly important given the impending expiration of Secure Boot certificates beginning in June 2026, which could impact system boot capabilities if not addressed proactively.
Additionally, the update strengthens Windows System Image Manager by improving the reliability of trusted catalog file selection and introducing a warning dialog that validates file sources before use. These enhancements address security vulnerabilities documented in the March 2026 Security Updates and the Security Update Guide. The servicing stack component receives quality improvements to ensure robust and reliable update delivery mechanisms. Organizations should prioritize installation to maintain security posture and prepare for upcoming certificate transitions.
General Sentiment
The overall sentiment toward KB5078766 is cautiously positive from a security perspective, as it addresses necessary vulnerabilities and prepares systems for critical infrastructure changes. However, there are important considerations that temper enthusiasm. The update introduces a known issue affecting Windows Server Update Services (WSUS) error reporting functionality, which was intentionally removed to address CVE-2025-59287, a Remote Code Execution vulnerability. This represents a trade-off between security and operational visibility that administrators must understand and accommodate.
The proactive approach to Secure Boot certificate management is viewed favorably, as it addresses a significant potential disruption point occurring in June 2026. However, the limited diagnostic data available for server environments means servers are unlikely to receive certificates automatically, requiring manual intervention or alternative deployment strategies. The combined SSU and LCU package approach is generally well-received as it simplifies deployment, though it does impose restrictions on selective uninstallation. The update demonstrates Microsoft's commitment to security hardening, though the WSUS functionality limitation may create temporary operational challenges for monitoring and troubleshooting update synchronization issues.
Known Issues
- Windows Server Update Services (WSUS) error reporting functionality is temporarily unavailable after installing KB5078766 or later updates. Synchronization error details are not displayed within WSUS error reporting interfaces due to remediation of CVE-2025-59287 (Remote Code Execution Vulnerability).
- Servicing stack updates (SSU) cannot be removed from the system after installation; only the cumulative update (LCU) component can be selectively uninstalled using DISM commands.
- Server systems are unlikely to automatically qualify for Secure Boot certificate distribution due to limited diagnostic data availability, requiring manual certificate management or alternative deployment approaches.
- Systems must have KB5030216 (September 12, 2023) or a later LCU installed before applying this update to offline OS images to prevent error 0x800f0823 (CBS_E_NEW_SERVICING_STACK_REQUIRED).
Disclaimer: We take measures to ensure that AI-generated content is of the highest possible quality, but we cannot guarantee its accuracy and recommend that users do their own independent research. Generated on 2026-04-28 01:41 PM