Stay Secure with NinjaOne Login Event Auditing
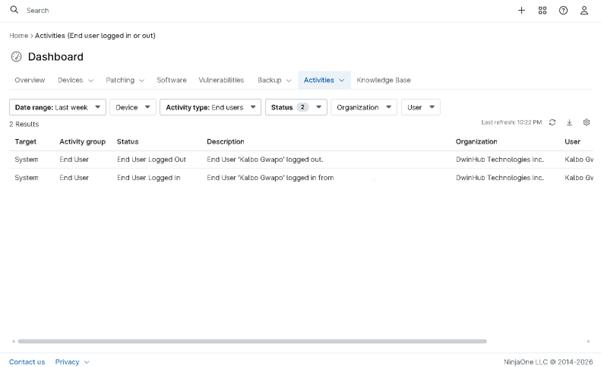
Knowing who logs in and when is critical to keeping IT environments secure. NinjaOne provides visibility into authentication activity across endpoints. IT teams can use this centralized view to monitor access patterns, investigate issues, and support compliance without searching through scattered logs. With clear insight into user activity, organizations can maintain better control and help ensure only authorized access.