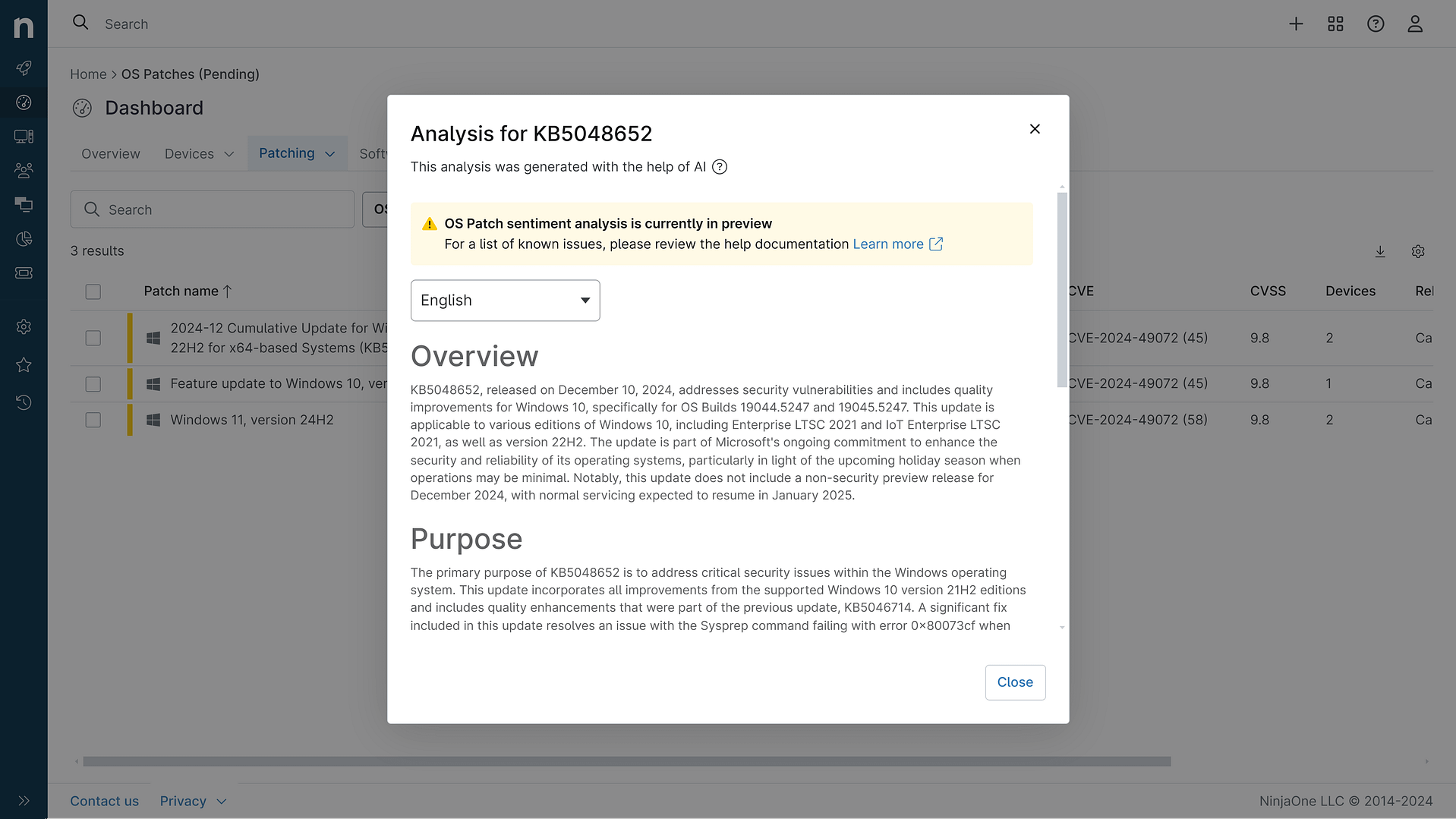
KB5087052: Overview with user sentiment and feedback
Last Updated May 13, 2026
Probability of successful installation and continued operation of the machine
Overview
KB5087052 is a cumulative security and reliability update released on May 12, 2026, targeting .NET Framework 3.5 and 4.8.1 on Microsoft Server Operating System version 23H2. This patch addresses critical security vulnerabilities while maintaining system stability through cumulative improvements to the .NET Framework runtime environment.
The update is distributed through multiple channels including Windows Update, Windows Update for Business, Microsoft Update Catalog, and Windows Server Update Services (WSUS), ensuring broad accessibility across enterprise and standard deployments. Microsoft explicitly recommends applying this update as part of regular maintenance routines to maintain security posture and operational reliability.
With no known issues reported at the time of release and a straightforward installation process, this patch represents a standard security maintenance cycle for organizations running the specified server operating system and .NET Framework versions.
General Purpose
KB5087052 delivers two critical security fixes addressing elevation of privilege vulnerabilities within the .NET Framework ecosystem. The first vulnerability, identified as CVE-2026-32177, represents a significant privilege escalation risk that could allow attackers to gain elevated system permissions. The second vulnerability, CVE-2026-35433, addresses a similar elevation of privilege threat within the same framework. These security improvements are essential for protecting server infrastructure from potential unauthorized access and privilege escalation attacks that could compromise system integrity and data security.
Beyond security enhancements, the update maintains cumulative reliability improvements to ensure stable operation of .NET Framework-dependent applications. The patch requires .NET Framework 3.5 or 4.8.1 to be pre-installed and necessitates a system restart following installation if affected files are actively in use. Microsoft recommends closing all .NET Framework-based applications prior to installation to minimize disruption and ensure clean application of the security patches.
General Sentiment
The sentiment surrounding KB5087052 is decidedly positive, driven by the absence of reported issues and the straightforward nature of the security fixes being applied. The patch addresses genuine security vulnerabilities without introducing apparent complications or compatibility concerns, which represents the ideal scenario for enterprise patch management. The update follows standard security update protocols with clear prerequisites and restart requirements, allowing IT professionals to plan deployments methodically.
However, some cautious considerations warrant mention. The patch targets a specific server operating system version (23H2) and specific .NET Framework versions, meaning organizations running different configurations will need to verify applicability before deployment. While no known issues exist at release, the cumulative nature of the update means it encompasses changes from multiple iterations, and edge cases in specific application environments could theoretically emerge post-deployment. Additionally, the requirement for system restart and application closure during installation necessitates proper change management and scheduling to avoid unplanned downtime in production environments. The lack of quality and reliability improvements beyond security fixes suggests this is purely a security-focused release rather than a comprehensive maintenance update.
Known Issues
- No known issues reported at time of release
- Microsoft has not identified any compatibility problems or operational disruptions associated with this update
Disclaimer: We take measures to ensure that AI-generated content is of the highest possible quality, but we cannot guarantee its accuracy and recommend that users do their own independent research. Generated on 2026-05-13 07:21 PM