KB5082404: Overview with user sentiment and feedback
Last Updated May 21, 2026
Probability of successful installation and continued operation of the machine
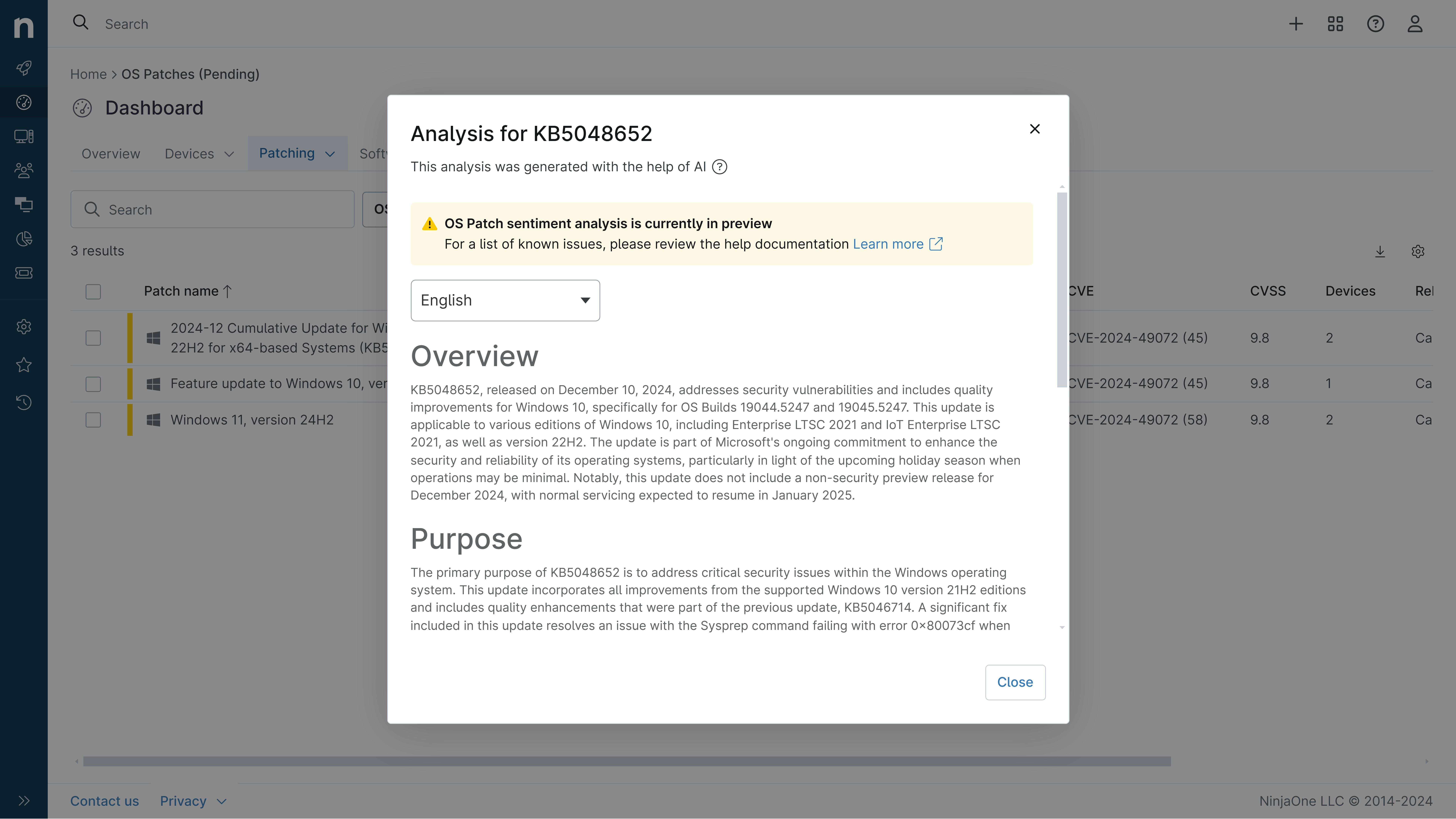
Overview
KB5082404 is an April 2026 Security and Quality Rollup update specifically designed for .NET Framework 4.8 running on Windows Server 2012 R2. This cumulative update addresses multiple critical security vulnerabilities and includes reliability improvements to the .NET runtime environment. The patch is particularly significant as it supports Extended Security Updates (ESUs) for Windows Server 2012 R2, which reached end of support on October 10, 2023. Organizations maintaining legacy server infrastructure can continue receiving security protections through this ESU program until October 13, 2026. The update encompasses six distinct CVE vulnerabilities ranging from remote code execution threats to denial-of-service exposures, alongside quality enhancements for ClickOnce deployment verification.
General Purpose
This security rollup addresses critical vulnerabilities within the .NET Framework 4.8 ecosystem on Windows Server 2012 R2. The primary security focus includes remediation of a remote code execution vulnerability (CVE-2026-32178) that could allow attackers to execute arbitrary code through the .NET runtime, along with multiple denial-of-service vulnerabilities (CVE-2026-32203, CVE-2026-32226, CVE-2026-23666) that could disrupt service availability. Additionally, the patch resolves a security feature bypass vulnerability (CVE-2026-26171) and an information disclosure vulnerability (CVE-2026-33116). Beyond security fixes, the update enhances the .NET runtime with improved ClickOnce deployment verification logic to support SHA384 and SHA512 hashing algorithms, modernizing cryptographic support for application deployment scenarios. The patch represents a comprehensive maintenance release combining threat mitigation with functional improvements for organizations dependent on legacy .NET Framework versions.
General Sentiment
Community sentiment regarding KB5082404 appears cautiously positive, though limited discussion volume suggests this is a routine maintenance release for a legacy platform. The update addresses genuine security threats with appropriate CVE documentation, which is viewed favorably by security-conscious administrators. However, some concerns exist regarding the deployment context: Windows Server 2012 R2 is an end-of-support operating system, and while ESUs provide extended protection, organizations should recognize this as a temporary measure rather than a long-term strategy. The patch includes a notable caveat regarding Azure Arc-enabled devices, where installation may fail without proper network endpoint configuration, which could create deployment friction in hybrid cloud environments. Conversely, the inclusion of ClickOnce improvements demonstrates Microsoft's commitment to maintaining functional compatibility even for aging platforms. The general sentiment leans toward acceptance as a necessary security update, though experienced administrators recognize this reflects the broader reality of maintaining legacy infrastructure rather than enthusiasm for the platform itself.
Known Issues
- Installation of this Extended Security Update may fail on Azure Arc-enabled devices running Windows Server 2012 R2 unless all required network endpoints for ESU are properly configured as documented in Connected Machine agent network requirements
- Language pack installation after applying this update requires reinstallation of the patch to maintain consistency
- Computer restart may be required if any affected .NET Framework files are in active use during installation
Disclaimer: We take measures to ensure that AI-generated content is of the highest possible quality, but we cannot guarantee its accuracy and recommend that users do their own independent research. Generated on 2026-05-21 07:26 PM