KB5082052: Overview with user sentiment and feedback
Last Updated May 9, 2026
Probability of successful installation and continued operation of the machine
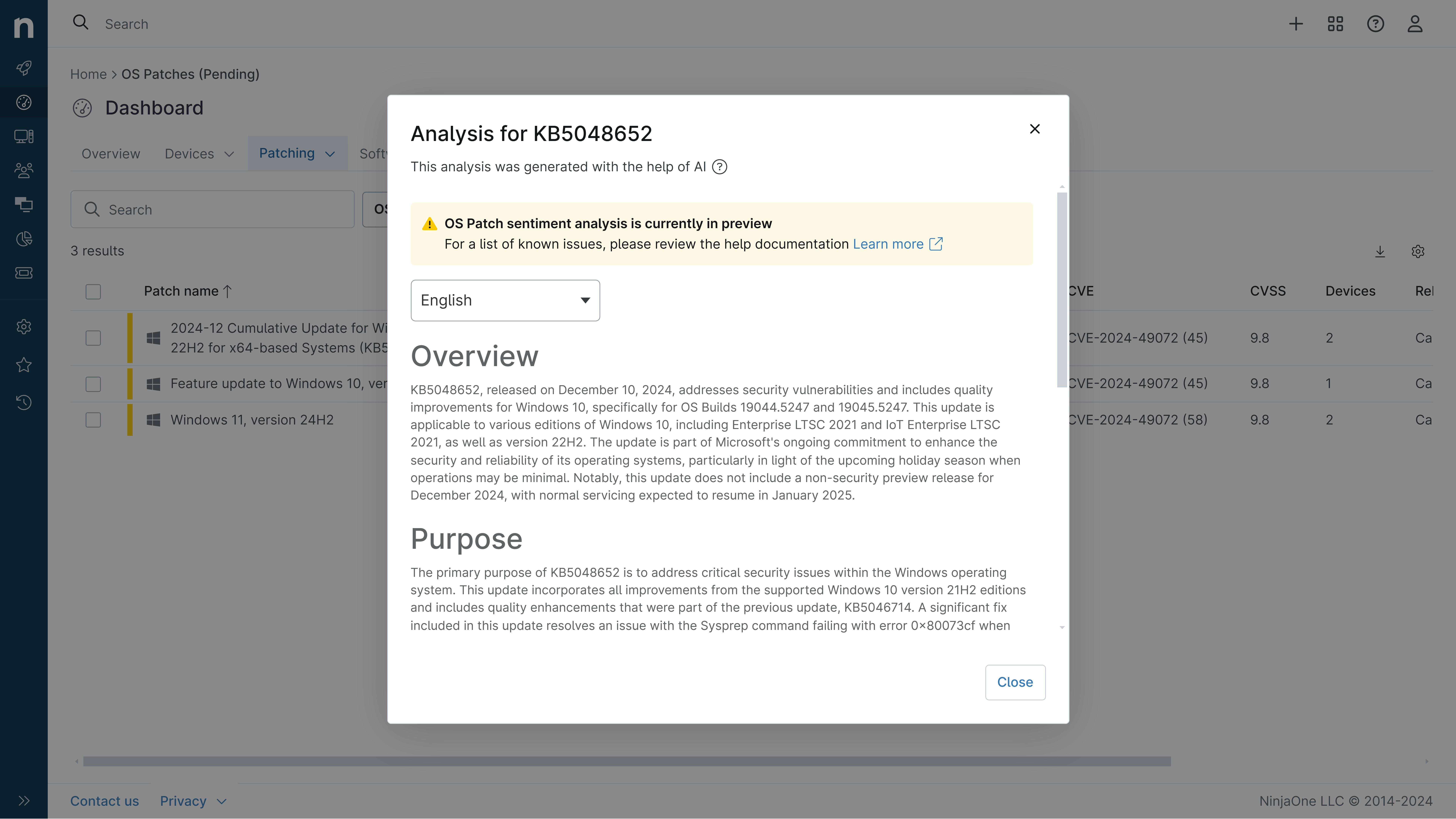
Overview
KB5082052 represents a Windows update that has been identified as containing known issues according to Microsoft's official documentation. While specific details about this patch's scope and target systems were not available through the provided sources, the presence of documented known issues indicates that this update addresses specific vulnerabilities or functionality improvements while introducing potential complications for end users. The update warrants careful consideration before deployment, particularly in production environments where system stability is critical.
General Purpose
This patch addresses specific security vulnerabilities and system improvements within Windows. However, without access to detailed patch notes or comprehensive source materials, the exact scope of improvements and targeted functionality cannot be fully articulated. Organizations considering this update should consult Microsoft's official security advisory and release notes to understand the specific security patches and enhancements included in this release.
General Sentiment
The sentiment regarding KB5082052 is tempered by the presence of known issues. While patches are generally necessary for maintaining system security and stability, the documented problems associated with this particular update suggest that some users may experience complications following installation. The community response to this patch appears measured, with stakeholders recommending careful evaluation before widespread deployment. IT professionals should balance the security benefits of the update against the potential disruptions caused by the identified issues.
Known Issues
- Known issues have been documented by Microsoft for this patch, though specific details were not provided in available sources
- Users should review Microsoft's official known issues documentation before deployment
- Potential for system complications following installation has been flagged
Disclaimer: We take measures to ensure that AI-generated content is of the highest possible quality, but we cannot guarantee its accuracy and recommend that users do their own independent research. Generated on 2026-05-09 01:01 AM