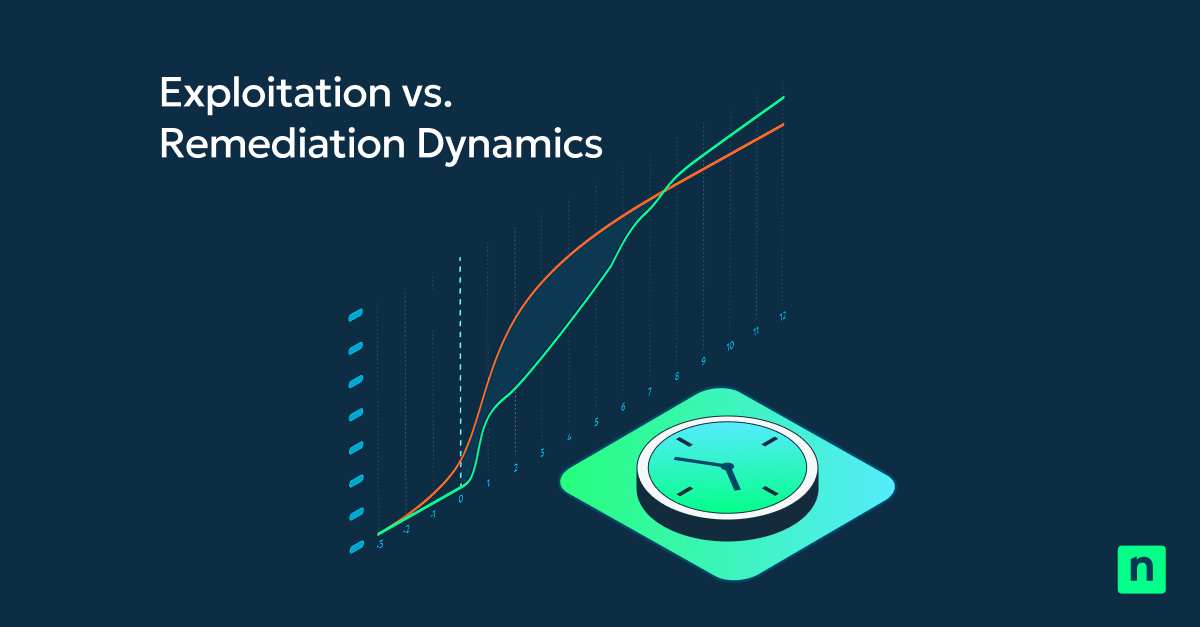
Every vulnerability creates exposure that doesn’t begin at patch deployment. It begins the moment a vulnerability becomes exploitable. By the time a vulnerability is publicly disclosed and a patch becomes available, attackers are already active. Yet organizations still rely on periodic scans to identify risk. The delay between vulnerability disclosure and remediation creates an operational exposure gap. This is the period when systems remain vulnerable while attackers are already moving.
Traditional vulnerability management isn’t built to accommodate the fact that attackers operate faster than ever. Attackers benefit from a process that requires IT teams to review findings, assess risk, and then build a remediation plan.
NinjaOne Vulnerability Management addresses this challenge with an integrated approach to identifying, prioritizing, and remediating vulnerabilities using AI-powered real-time assessment. In this blog, we’ll look at how this shift helps IT and security teams move from reactive, scheduled scans to continuous, up-to-date vulnerability visibility.
Why scan-driven vulnerability management falls short
Most vulnerability management tools operate on schedules. Endpoints are evaluated at fixed intervals, frequently scheduled outside business hours to avoid disrupting end-user productivity. Reports with findings are compiled and passed from the Security team to the IT Ops team for remediation. This model introduces friction because discovery and remediation occur in separate tools and workflows which results in patching delays.
This results in organizations spending an unnecessary amount of time vulnerable. Remediation can be delayed by days, weeks, and even months. In fact, according to Verizon’s Data Breach Investigations Report, only 54 percent of vulnerabilities were remediated within 32 days. The longer the delay, the higher the risk. Unfortunately, threats emerge continuously, so waiting days or weeks for the next scan or report handoff between SecOps to IT Ops simply isn’t good enough.
A new approach: AI-powered, real-time vulnerability assessment
NinjaOne Vulnerability Management with AI-powered, real-time assessment eliminates scan dependency. Instead of point-in-time scans, NinjaOne leverages AI-powered continuous correlation and matches live and last-known endpoint software state with current CVE intelligence. As endpoints change, software is updated, or patches are applied, vulnerability status updates automatically, ensuring IT has near immediate visibility into vulnerability exposure. Teams no longer have to wait for scan cycles that are further slowed by process handoffs.
In addition, because NinjaOne Vulnerability Management identifies and automatically patches vulnerabilities as they appear, when Security does run their scan, it will show fewer issues. Those that are reported would be of higher importance and easier to prioritize for remediation because the IT OPs team is not burdened by a large number of vulnerabilities.
Continuous visibility: even when devices are offline
If a new CVE is published while a device is offline, NinjaOne matches that vulnerability to the device’s last-known software state. Exposure intelligence is preserved and queued for action the moment the endpoint reconnects. This eliminates scan-time blind spots and ensures continuous awareness across uptime gaps
Key benefits of NinjaOne Vulnerability Management Real-Time Assessment
- Always-accurate visibility
- With AI-driven, real-time assessment, you no longer need to rely on scanning schedules and inefficient process handoffs.
- Smarter prioritization
- NinjaOne helps you focus on the most important issues by linking vulnerabilities to endpoints allowing IT to tackle the highest risks first.
- Tightly integrated with patching
- Effective vulnerability management works if fixes happen quickly. NinjaOne combines finding vulnerabilities and patching them into one platform.
- Reduced operational overhead
- NinjaOne removes the need for manual scans, exporting reports, and switching between tools, making daily work easier. You’ll spend less time managing tools and more time reducing risk.
- Deep scanning verification layer
- Ingest findings from existing vulnerability scanners, like Tenable, Qualys, and Rapid7 into NinjaOne to accelerate remediation execution without replacing current discovery tools.
- Scales with modern IT environments
- Whether you’re managing hundreds or thousands of endpoints, real-time assessment ensures consistent visibility across distributed, remote, and hybrid environments.
Why real-time assessment changes everything
By closing the gap between the time a vulnerability is discovered and when it’s remediated, real-time assessment allows you to deliver effective patching outcomes instantly, respond more quickly to emerging threats, and maintain a vastly improved security posture.
Instead of reacting to reports, your team operates with continuous exposure intelligence.
Built for IT Operations
NinjaOne Vulnerability Management is built for modern IT environments. It’s intuitive, automated, and fully integrated into the NinjaOne platform. This enables you to manage vulnerabilities without adding another tool to your technology stack.
With real-time assessment, autonomous patch management, and endpoint control all in one place, NinjaOne helps you move from reacting to problems to proactively reducing risk.
The future of vulnerability management starts now
Threat velocity isn’t slowing down. Vulnerability management must move at the speed of risk. With NinjaOne Real-Time Assessment, you close the operational exposure gap without creating new operational risk. The future isn’t more scans. It’s continuous, AI-powered, actionable visibility.
Learn more about NinjaOne Vulnerability Management.