NinjaOne Secure Containerization for Android Devices
Protect your business data without compromising user privacy using NinjaOne’s secure containerization for Android. Designed for modern BYOD environments, this secure containerization tool creates a dedicated workspace on employee-owned devices, separating personal and corporate data. With centralized control, encrypted storage, and seamless app deployment, NinjaOne simplifies the secure containerization process for IT teams.
Whether you’re managing a few devices or scaling across a global workforce, NinjaOne enables secure separation of work and personal data on Android devices, ensuring performance, compliance, and ease of use.
Why Secure Containerization with NinjaOne Matters
Isolated Workspaces for Corporate Data
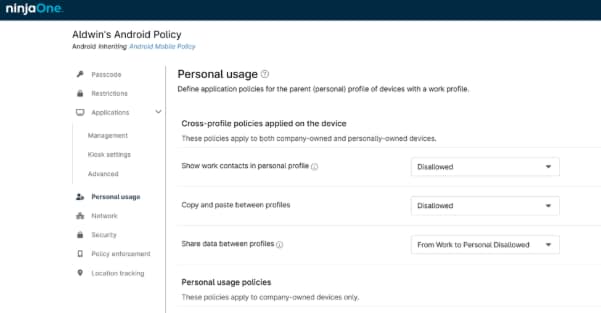
Granular Policy Enforcement
Remote Wipe for Business Data Only
Streamlined App Management
Enhanced User Privacy and Experience
Purpose-built tools for Android BYOD security
Work Profile Isolation
Remote Container Management
App Whitelisting and Blacklisting
Data Encryption at Rest and in Transit
Seamless User Onboarding
Real-world applications for Android BYOD environments
BYOD Security for Hybrid Workforces
Organizations embracing BYOD can confidently allow Android devices with NinjaOne’s secure containerization tool. Employees access work apps in a protected containerized environment, while IT maintains full control over business data. This secure containerization process ensures that personal apps remain untouched, preserving user privacy and device usability. NinjaOne’s secure containerization management allows IT teams to enforce policies and perform remote actions without disrupting personal content. With containerization in cyber security becoming a standard, NinjaOne’s solution supports compliance and data protection across distributed teams. Perfect for hybrid environments, where secure access and user privacy must go hand in hand.
Data Protection in Regulated Industries
Healthcare, finance, and legal sectors benefit from NinjaOne’s secure containerization solution for Android, which isolates and encrypts sensitive data. The secure containerization environment ensures that business apps operate within a protected space, reducing the risk of data breaches. IT teams can use container security features to enforce granular controls and monitor compliance in real time. NinjaOne’s secure containerization software supports containerization in cyber security standards like HIPAA and GDPR, making it easier to meet regulatory requirements. The secure containerization management tools also allow for remote updates and selective wipes, ensuring business continuity. This secure containerization tool is essential for regulated industries that demand high levels of data protection and operational efficiency.
Efficient Offboarding and Device Recovery
Take Control of Android BYOD with NinjaOne.
NinjaOne’s secure containerization for Android empowers IT teams to protect business data, streamline app management, and support user privacy—all from a single platform. Whether you’re enabling remote work, securing sensitive data, or simplifying compliance, NinjaOne delivers a secure containerization solution that’s built for performance and scale.
Try it today and experience the future of containerization in cyber security.
Secure Containerization FAQs
What is secure containerization in MDM?
Secure containerization in MDM refers to the use of a secure containerization tool to create an isolated workspace on a mobile device. This container separates business apps and data from personal content, allowing IT to manage and secure corporate information without interfering with the user’s personal experience.
What is containerization in cyber security?
Containerization in cyber security is the practice of isolating applications and data within a secure, controlled environment, often leveraging containerization security best practices. This approach enhances security by preventing unauthorized access and ensuring that sensitive data remains protected, especially on mobile devices.
Why is secure containerization important for mobile device management?
Secure containerization is essential for mobile device management because it allows organizations to enforce security policies, manage business apps, and protect data on employee-owned devices. It supports BYOD strategies while maintaining compliance and user privacy.
How does NinjaOne support secure containerization?
NinjaOne offers a secure containerization solution for Android that includes remote management, policy enforcement, app control, and selective wipe capabilities. It integrates with NinjaOne’s broader MDM platform to provide a seamless and secure containerization process.
Which operating systems support secure containerization?
Currently, NinjaOne’s secure containerization software supports Android devices, leveraging Android’s native work profile to create a secure containerized environment.
Can users still access personal apps on containerized devices?
Yes. The secure containerization environment only affects the work profile, allowing users to continue using personal apps and data without interference.
Is data inside a secure container encrypted?
Yes. NinjaOne’s secure containerization tool ensures that all data within the container is encrypted at rest and in transit, providing strong container security.
Can admins wipe only the business data from a device?
Absolutely. With NinjaOne’s secure containerization management, IT can perform a selective wipe that removes only the business data inside the container, leaving personal content untouched.
Does secure containerization affect device performance or usability?
No. The secure containerization software is designed to run efficiently in the background, with minimal impact on device performance or user experience.
How does containerization compare to full device management?
Containerization offers a more flexible and privacy-conscious approach than full device management. It focuses on securing business data within a containerized environment, making it ideal for BYOD scenarios.
Is secure containerization required for compliance?
While not always mandatory, secure containerization significantly helps organizations meet compliance requirements by isolating and protecting sensitive data, especially in regulated industries.
Related Resources
BYOD Security Guide: Top Threats & Best Practices
Learn how to secure personal devices in the workplace and protect corporate data seamlessly.
Data Protection Methods for IT & MSP Teams
What is Mobile Device Management?
