KB5082142: Overview with user sentiment and feedback
Last Updated May 30, 2026
Probability of successful installation and continued operation of the machine
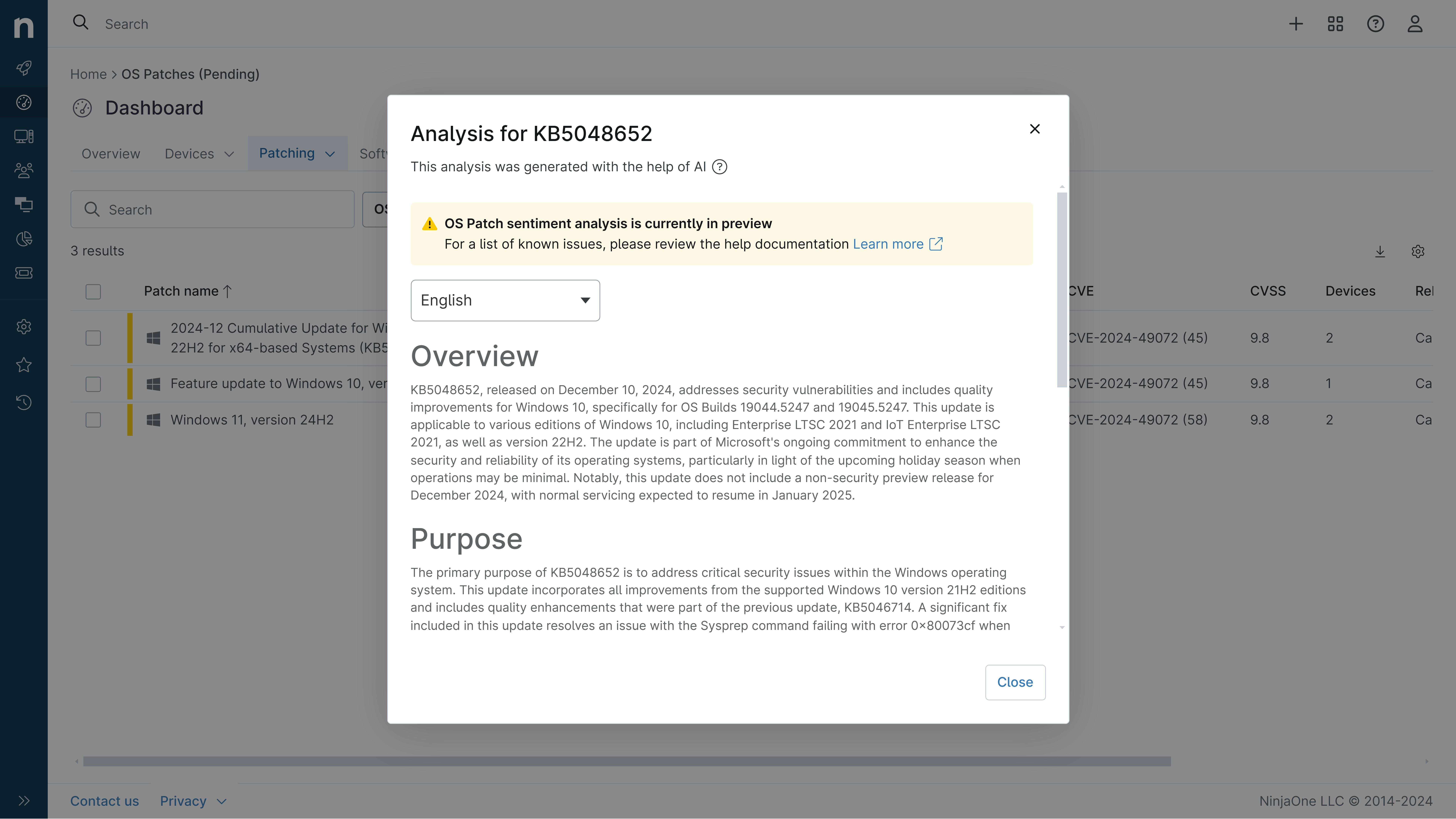
Overview
KB5082142 is the April 2026 cumulative security update for Windows Server 2022, released on April 14, 2026, with OS Build 20348.5020. This update represents Microsoft's monthly rollup of security patches and quality improvements, incorporating fixes from the previous month's optional preview release (KB5078766 from March 10, 2026). The update addresses multiple security vulnerabilities and introduces quality enhancements across various system components including connectivity, kernel stability, networking protocols, and security features.
This cumulative update is distributed through multiple channels including Windows Update, Windows Update for Business, and Windows Server Update Services (WSUS). The update combines both the servicing stack update (SSU KB5082137, version 20348.5021) and the latest cumulative update into a single package, streamlining the deployment process. Organizations should be aware that this update includes several notable changes, particularly around security hardening measures and certificate management related to upcoming Secure Boot certificate expirations in June 2026.
General Purpose
KB5082142 delivers comprehensive security and stability improvements across Windows Server 2022 infrastructure. The update enhances audio reliability and system responsiveness by reducing interruptions during sound-related operations. Kernel-level improvements strengthen system stability during large file operations, allowing users to work with and transfer substantial data volumes with fewer unexpected interruptions.
Networking capabilities receive significant attention, with improved reliability for SMB compression over QUIC protocol, resulting in more consistent request completion and reduced timeout occurrences. The update strengthens Remote Desktop security by implementing enhanced protection against phishing attacks using RDP files, displaying all connection settings before establishing connections with security warnings enabled by default.
Kerberos protocol handling has been refined to leverage AES-SHA1 encryption for Key Distribution Center operations on accounts lacking explicit encryption type definitions, addressing CVE-2026-20833. Security hardening extends to the addition of known vulnerable kernel drivers to Microsoft's blocklist, though this may impact certain backup applications relying on older drivers. The update also disables Windows Deployment Services Hands-Free Deployment feature by default for security reasons and improves Secure Boot certificate distribution with enhanced device targeting capabilities.
General Sentiment
Community reception of KB5082142 presents a mixed picture with significant concerns emerging from real-world deployments. While Microsoft's official documentation emphasizes security improvements and stability enhancements, field reports indicate potentially serious complications affecting infrastructure operations. The update has garnered attention on technical forums, particularly regarding network infrastructure components, suggesting that despite security benefits, administrators should approach deployment with caution.
Positive aspects include the comprehensive security updates addressing multiple vulnerabilities and the phased rollout approach for Secure Boot certificates, which demonstrates Microsoft's attempt to manage deployment risk. However, community feedback reveals disruptions affecting critical infrastructure components. The vulnerable driver blocklist, while security-focused, creates compatibility challenges for backup solutions and specialized applications. Some administrators report that the update introduces instability in configurations previously operating reliably for extended periods, particularly affecting domain controller environments and network teaming scenarios. The presence of multiple known issues documented by Microsoft, combined with community reports of undocumented problems, suggests this update warrants careful pre-deployment testing and staged rollout strategies rather than immediate enterprise-wide deployment.
Known Issues
- Domain controllers in multi-domain forests using Privileged Access Management (PAM) may experience LSASS crashes during startup, causing repeated restarts and rendering domains unavailable. Resolution available through out-of-band update KB5091575 or hotpatch KB5091576 for enrolled devices.
- Devices with specific BitLocker Group Policy configurations (PCR7 inclusion in TPM validation profile) combined with Windows UEFI CA 2023 certificate presence may require BitLocker recovery key entry on first restart. Workaround involves removing the Group Policy configuration before installation or suspending/resuming BitLocker protection.
- Windows Server Update Services (WSUS) no longer displays synchronization error details following installation, a temporary measure to address CVE-2025-59287 remote code execution vulnerability.
- Remote Desktop security warnings may display incorrectly on systems with multiple monitors using different display scaling settings, potentially showing overlapping text or hidden buttons. Resolution addressed in KB5087545.
- Backup applications relying on blocked vulnerable kernel drivers may experience failures when mounting or managing disk images, displaying errors such as "The backup has failed because Microsoft VSS has timed out during the snapshot creation" or VSS_E_BAD_STATE.
- NIC Teaming configurations may become disabled or faulted following installation, with member NICs showing as "Faulted Not Found" and default gateways being removed, requiring manual reconfiguration.
Disclaimer: We take measures to ensure that AI-generated content is of the highest possible quality, but we cannot guarantee its accuracy and recommend that users do their own independent research. Generated on 2026-05-30 01:57 PM