By its very nature, shadow IT is often unseen by IT security teams. This oversight routinely risks organizations violating data privacy laws, distorting IT budgets, and being exposed to nefarious actors. In a remote work environment, shadow IT poses a new threat that must be actively managed.
→ Download your free Shadow IT Report [PDF]
What is shadow IT?
Shadow IT is the practice of using information technology systems that an organization’s IT department does not manage. This can be anything from using an unsanctioned personal device to downloading software or applications that the IT department does not approve.
Understanding shadow IT behaviors
The rise of unconventional work setups that have become normalized in recent years has created many challenges for businesses and organizations. One is ensuring the company’s data is protected from breaches and unauthorized access. Providing sanctioned devices can establish a baseline level of control. However, some hurdles still exacerbate the risks associated with shadow IT. These hurdles encompass IT behaviors displayed by employees themselves that contribute to the risks brought by shadow IT.
Examples of shadow IT practices
To give you a better overview of shadow IT, here are some common shadow IT examples:
- Downloading unapproved software. While it may seem harmless to download and install software and applications from an official software distributor, this doesn’t mean that it’s completely secure. Some software will ask users to grant permission to access sensitive data, system resources, network connections, etc. One wrong click granting these permissions can lead to data breaches, compliance violations, or even malware infections.
- Sharing login credentials. Another practice with a clear security breach risk is sharing login credentials. Usernames and passwords are not supposed to be shared with anyone else. Doing this can easily compromise the security of the user’s accounts and open the door to potential misuse.
- Using personal devices for work. More and more companies have started providing employees with devices they should use exclusively for work. However, some employees still use their personal devices despite the potential security risks. This poses a risk of exposing company data to malware or compromising personal data through work applications.
- Using unauthorized cloud storage services. Employees get tempted to use cloud storage services that they can easily access. This cloud storage that the company does not authorize poses a significant security risk. They may even cause loss of critical company data, leading to operational disruptions, reputational damage, and significant financial penalties.
- Utilizing unauthorized communication tools. Sharing confidential information through communication tools not approved by your organization may cause serious breaches of security protocols and compromise sensitive data.
Factors leading to shadow IT adoption
There are several reasons that drive users to adopt shadow IT practices. One is the perceived inefficiency or inadequacy of approved tools provided by the organization. This results in users looking for alternative IT systems to ease their workflow. Another one is the lengthy process of acquiring official IT solutions, which drives users to opt for unauthorized tools for quicker access to necessary functionalities.
In some cases, productivity also drives users to use unsanctioned IT systems. Some may find themselves more productive when using their personal devices that they’re already used to navigating. Others may utilize software that offers specific features or functionalities lacking in approved software, potentially leading to increased efficiency and productivity gains.
Lastly, the users’ lack of awareness about security risks associated with shadow IT can lead to further adoption of shadow IT practices. Without proper knowledge about the implications of shadow IT behavior, they may unknowingly expose sensitive company data.
The negative implications of shadow IT usage
Since we’ve uncovered motivations for shadow IT adoption, it’s crucial to delve into the dangers it may cause an organization. As we’ve mentioned, shadow IT practices pose risks of information breach and data loss. This is why a recent study by Entrust revealed that 77% of IT professionals are concerned about shadow IT becoming a significant issue in 2023. It’s an inevitable consequence of the emergence of remote work and hybrid employment setup.
Shadow IT can also expose IT infrastructures to apparent vulnerabilities. Software and devices that are not authorized typically lack security patches and updates implemented by companies. This can create potential entry points for malware and cyberattacks, compromising the entire network that may lead to widespread disruptions, data, and financial losses.
The pros and cons of shadow IT usage
It’s easy to avoid shadow IT practices if they only bring negative consequences. However, the reality is that shadow IT can offer some user-end benefits alongside its significant risks.
Pros:
- Employee satisfaction. Utilizing unauthorized tools that may aid in expediting workflow can ease an employee’s burdens.
- Increased productivity. When a user is satisfied with the unsanctioned IT system they’re using, it can potentially lead to increased efficiency and productivity gains.
- Innovation introduction. Using unapproved IT systems may lead to the discovery of more innovative tools and efficient ways of completing tasks.
- Flexibility and adaptability. Shadow IT allows users to utilize tools they are familiar with and comfortable using. This reduces a steep learning curve and can increase efficiency.
- Collaboration. Shadow IT practices involving unauthorized communication channels may promote a more efficient collaboration among users.
- Personalization. Shadow IT tools may offer more personalization than standardized, one-size-fits-all solutions provided by the IT department.
Cons:
- Exposure to vulnerabilities. Shadow IT tools are easy targets for cyberattacks because they often lack security features and protocols implemented by an organization’s IT team.
- Non-compliance with regulations. Most organizations comply with industry regulations or data privacy laws. Shadow IT tools also frequently lack the essential safeguards to ensure compliance, putting the organization at significant risk.
- Support hurdles. Sanctioned IT systems are in place to resolve any issues that may arise immediately. Shadow IT tools may not have complete dedicated support infrastructure, which can hinder technical issues from being resolved.
- Data loss. Shadow IT tools increase the risk of sensitive data loss due to the lack of data protection measures often found in unauthorized tools.
- Financial losses. Data breaches that are caused by the use of shadow IT tools can lead to revenue loss. This can be due to several factors, such as regulatory fines, incident response costs, operational downtime, etc.
- Version control issues. Multiple versions of unauthorized software used across the organization can create compatibility problems and hinder collaboration.
FAQ
How to detect shadow IT?
– There are multiple approaches when it comes to detecting shadow IT practices. Looking for unauthorized software downloads is one of them. Unusual network activities may also signal a shadow IT behavior. Another one is the reduced usage of a sanctioned device. These can all be potential signs of shadow IT behavior within an organization.
What is a good reason for a shadow IT team to arise within an organization?
– The rise of shadow IT practices may be prompted by several factors, such as inefficient approved IT systems, lengthy setup and approval processes, or the reduction of productivity when utilizing systems authorized by the IT team.
What should you do to identify if shadow IT is present in your company?
– If you work for an organization’s IT department, the first thing you need to do is risk assessment by determining the severity of the situation and how widespread the shadow IT practice is at that moment. Next is identifying the employees’ motivations to understand their needs with approved solutions. Then, leverage employee training and emphasize the importance of using approved IT systems. Finally, existing policies regarding shadow IT practices should be communicated.
What is shadow IT in cybersecurity?
– Shadow IT is the terminology used to describe the use of IT-related systems that are not approved or sanctioned by an organization’s IT team. It encompasses hardware, software, cloud services, and more.
What best describes an insider threat?
– Insider threat is the perceived threat from people who have or had access to critical company information that they can use to harm that organization.
What we do in the shadows: The dangers of hidden IT behavior
To better understand the shadow IT behaviors of employees working remotely due to COVID-19, NinjaOne surveyed 400 remote workers in the UK across multiple industries. We learned that while the majority of respondents were indeed aware of their organization’s security policies, employees will often skirt the rules, using an array of physical devices like hard drives and smartphones and digital tools like communication and business software.
We learned that while the majority of respondents were indeed aware of their organization’s security policies, employees will often skirt the rules, using an array of physical devices like hard drives and smartphones and digital tools like communication and business software. Recommendations based on the survey results suggest frequent security training combined with clear policies and frictionless IT experiences can reduce or eliminate some of the reasons employees turn to shadow devices and applications in the first place.
In the remote work era, full management of devices interacting with company data should be in place. It’s the job of leadership to understand the needs and obstacles of their team and set the tone and policies regarding basic security hygiene.
To learn more about how shadow IT is impacting the organization and how to turn these security gaps into opportunities, download our full report.
Download your shadow IT report
to learn more about the dangers of hidden IT behavior ☠️
Managing shadow IT behavior
With the emergence of hybrid and remote work setups, some employees find IT shadow tools beneficial. However, the benefits of these unauthorized IT systems are frequently short-term. While it can be challenging for organizations to fully eradicate shadow IT practices, there are ways to manage and mitigate risks. An endpoint management system, such as NinjaOne, can be a perfect ally in this endeavor.
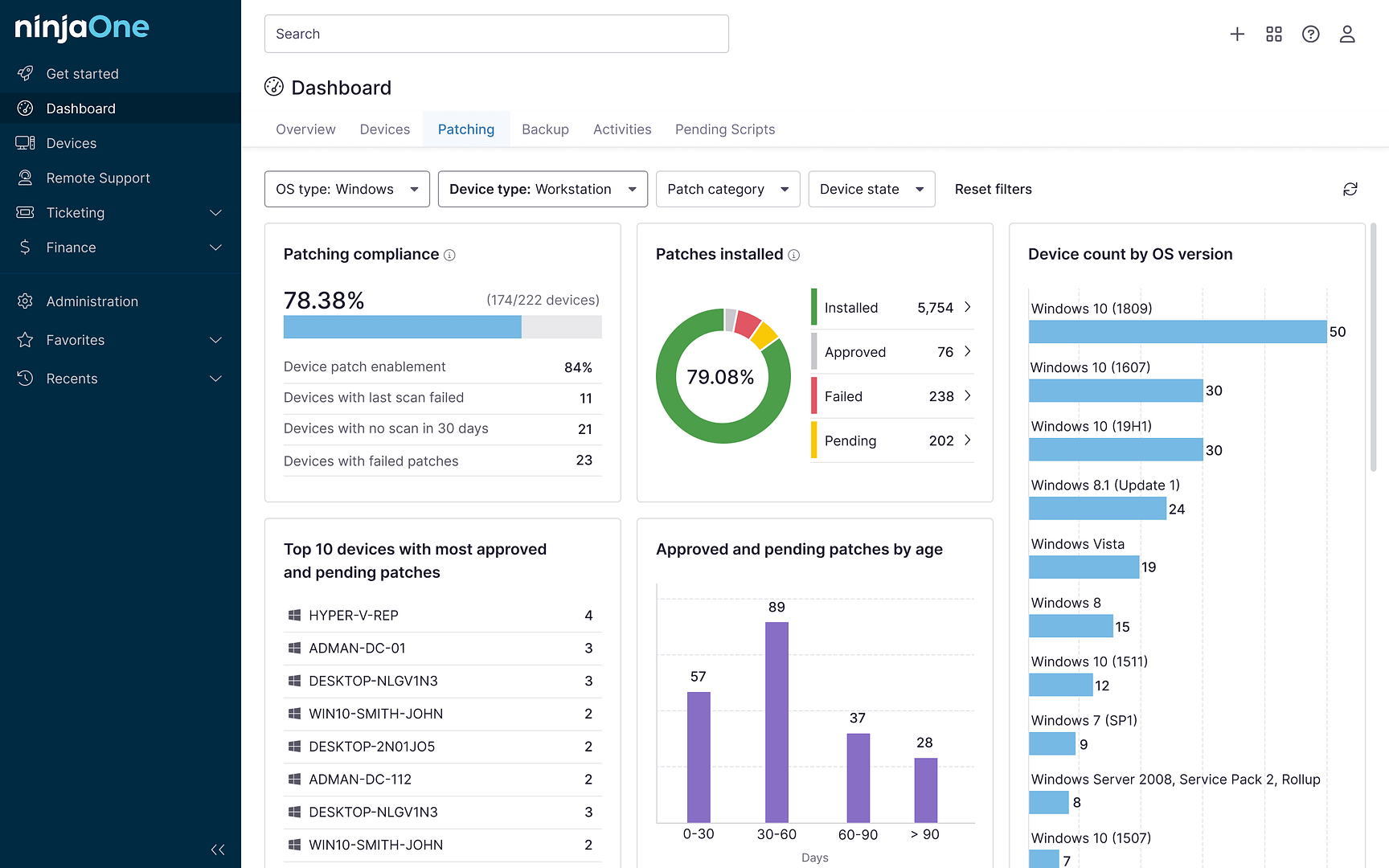
NinjaOne empowers IT teams to manage and mitigate shadow IT behavior. Its features grant real-time visibility over your network, automate tasks, and enforce security policies while providing user-friendly access to approved IT solutions, ultimately boosting security and employee satisfaction. This fosters a secure and productive work environment that empowers employees while safeguarding critical data and assets.