The Growing Role of AI in Endpoint Management and Security Convergence

The Growing Role of AI in Endpoint Management and Security Convergence A Report from Enterprise Strategy Group Download Now More endpoints, increasing tool sprawl, and technician skill gaps contribute to unmanaged devices and a higher risk of cyber threats. This Enterprise Strategy Group report looks at the rise in endpoint management complexity along with the […]
The Worst-Case Scenario Survival Guide: Vulnerability Remediation Edition
The Worst-Case Scenario Survival Guide:Vulnerability Remediation Edition How to Survive a Critical CVE and Other Cyber Catastrophes Download Now Critical CVEs don’t wait. Exploits don’t pause for testing. And your team can’t afford to patch under pressure. Download the The Worst-Case Scenario Survival Guide: Vulnerability Remediation Edition and get a practical, high-impact playbook for surviving […]
DORA Compliance Guide
DORA – Ensuring BusinessContinuity and Operational Resilience with NinjaOne A Practical Guide to Navigating DORA Compliance Challenges Download Now Learn how NinjaOne helps financial institutions tackle the complex demands of the Digital Operational Resilience Act (DORA) while maintaining operational efficiency and business continuity. DORA introduces enforceable standards for managing ICT risk, monitoring threats, and securing […]
Building Cyber Resilience for NIS2 Readiness
Building Cyber Resiliencefor NIS2 Readiness A Guide to how NinjaOne can help you navigate NIS2 objectives Download Now This guide explains how NinjaOne can assist your organization to prepare better for NIS2 compliance. NinjaOne is a powerful tool in strengthening your organization’s cybersecurity posture by automating key processes and implementing robust security measures, thereby supporting […]
Building a Security First Reputation With NinjaOne

Own Your Security Future. Build A Security First Reputation With NinjaOne. Learn how to build a proactive security strategy and gain a competitive edge. Download Now Are you feeling pressure to safeguard your organization’s data and reputation? You’re not alone. Our free eBook, Building A Security First Reputation With NinjaOne, equips you with the knowledge […]
Ransomware: The Perils of Waiting to Backup

Ransomware: Don’t Be a Sitting Duck – Download Your Free Guide Protect Your Business with Secure Backups and Security Strategies Download now Are you prepared for a ransomware attack? One accidental click from an unsuspecting user and digital extortionists can immobilize your business, locking down critical information, demanding hefty ransoms, and leaving your company dead […]
Top 5 IT Security Fundamentals
The Top 5 IT Security Fundamentals Simple security hygiene can save you millions… and your job Download now IT doesn’t just deal with operations and up time, it has to ensure things are done in a secure manner. Data has become the new currency and technology the lifeblood of every organization, the need for robust […]
2023’s Top Vulnerabilities and The Power of Patch Management

MSP’s Hype-Free Guide to EDR Understanding and Evaluating Endpoint Detection & Response Tools Download Now This free 26-page guide answers all the questions you should be asking about EDR Successful cyber attacks are taking a toll on SMBs and MSPs, alike. With traditional security solutions failing to prevent compromises, the focus is on finding alternative solutions […]
2024 IT Priorities On-Demand Webinar

2024 IT Priorities: Automation, Security and Consolidation Lead the Way (Webinar On-Demand) Watch the Webinar About the Webinar In today’s shifting IT landscape, the need to prioritize key areas of investment for IT technology is crucial. Drawing from a comprehensive survey of over 600 IT experts conducted in collaboration with Omdia, this webinar offers a […]
Leading IT Trends for 2024: Embracing Automation, Security, and Consolidation

Leading IT Trends for 2024 2024 is expected to be a year of continued evolution within the world of IT, between an increased focus on automation, enhanced security processes to battle complex threats, and end-user productivity. In an effort to understand the unique challenges that IT will face in the year to come, NinjaOne has […]
A Warlock’s Guide to Selling Security Services

Learn the ways of selling cybersecurity in this handbook.
The Endpoint Defense Playbook
Lock down devices and automate security with NinjaOne.
Patch Management Buyer’s Guide for IT Directors
Is it time for a new patch management solution?
Endpoint Hardening Checklist
Get actionable endpoint hardening recommendations you can use to protect systems and reduce attack surface.
Jurassic SOC

Can you claw back control over the network on Isla Nublar? You’ll have one hour to find out.
Rogue WAN: A Data Breach Story

Can you hack it as the Empire’s new IT support? Join us on May the 4th at 2pm ET for a one-of-a-kind cybersecurity workshop.
Must-Know Ransomware Statistics and Attack Trends 2023
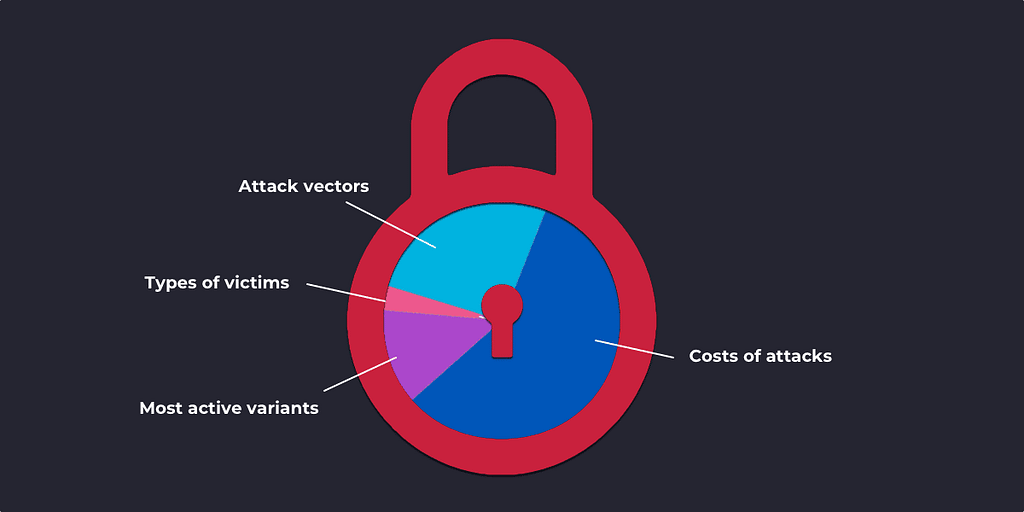
From massive increases in ransom amounts to big shifts in attack models, these statistics reveal the major new trends in ransomware.
Top Phishing Lures and Malicious Email Disguises to Watch Out For
Protect your clients from this year’s scariest scams and creepiest compromises by teaching them how to see through the most common malspam and phishing disguises.
6 Keys to Surviving a Ransomware Outbreak
With client-wide ransomware infections being reported on a weekly basis, MSPs need to need to be focusing on incident response planning now. Huntress Labs CEO Kyle Hanslovan shares the key lessons he’s learned firsthand from working with nearly 40 MSPs who have been compromised.
Surviving Ransomare Pt 3: Legal Risk & Cyber Insurance FAQs
MSP legal authority Bradley Gross teams up with techrug founder Justin Reinmuth to cover everything MSPs need to know about cyber insurance and lowering their legal risk associated with cyber attacks.