Svchost.exe, also known as Service Host, is a system process inherent to the Windows operating system that serves a pivotal role in hosting and managing one or more Windows services.
This process is instrumental in ensuring that various system services run smoothly and efficiently, segregating them into distinct groups to prevent service failures from affecting the entire system.
For both everyday users and IT professionals, understanding the role of svchost.exe is crucial. This guide is dedicated to providing a thorough exploration of svchost.exe, elucidating its purpose within the Windows operating system, and addressing prevalent concerns regarding its security.
It aims to enlighten readers on the intricacies of what is svchost.exe and its nature, detailing its functions and guiding them in discerning whether it is secure or potentially malicious.
What is svchost.exe?
Svchost.exe is a system process designed to host and manage DLL-based services. It enables multiple instances of itself to run simultaneously, each hosting a different group of services, thus optimizing the use of system resources and ensuring that services are organized based on their categories and security requirements.
In Windows operating systems, svchost.exe is essential for the smooth operation of the system by managing background services that are critical for both system performance and functionality. These services include networking, user interfaces, file management, and more.
Why there are multiple instances of svchost.exe running
- Efficiency in resource usage: Each instance of svchost.exe can run a set of services independently of others, which means if one instance fails, it doesn’t impact the services in another instance.
- Enhanced security: Separate instances allow for different security settings depending on the sensitivity of the services being run, thereby isolating more secure services from less secure ones.
- Scalability: Multiple instances allow Windows to scale the services horizontally as needed without overloading a single service host.
Functions of svchost.exe
Hosting Windows services
Svchost.exe loads services from DLL files into memory and runs them as part of its process. This helps in conserving system resources as these services share the same instance of svchost.exe.
Examples of services typically hosted by svchost.exe:
- DNS client: Manages DNS lookups and caching for quick internet access.
- Windows update: Handles the downloading and installation of Windows updates.
- Task scheduler: Enables the scheduling and automation of tasks within the operating system.
Resource management
- How svchost.exe manages system resources: By hosting multiple services within a single process, svchost.exe reduces the overall footprint of system resources required for running these services.
- Impact on system performance: Proper management ensures that no single instance consumes more resources than necessary, maintaining system stability and performance. Overloaded svchost.exe instances can however sometimes lead to high CPU or memory usage, impacting overall system performance.
Determining the safety of svchost.exe
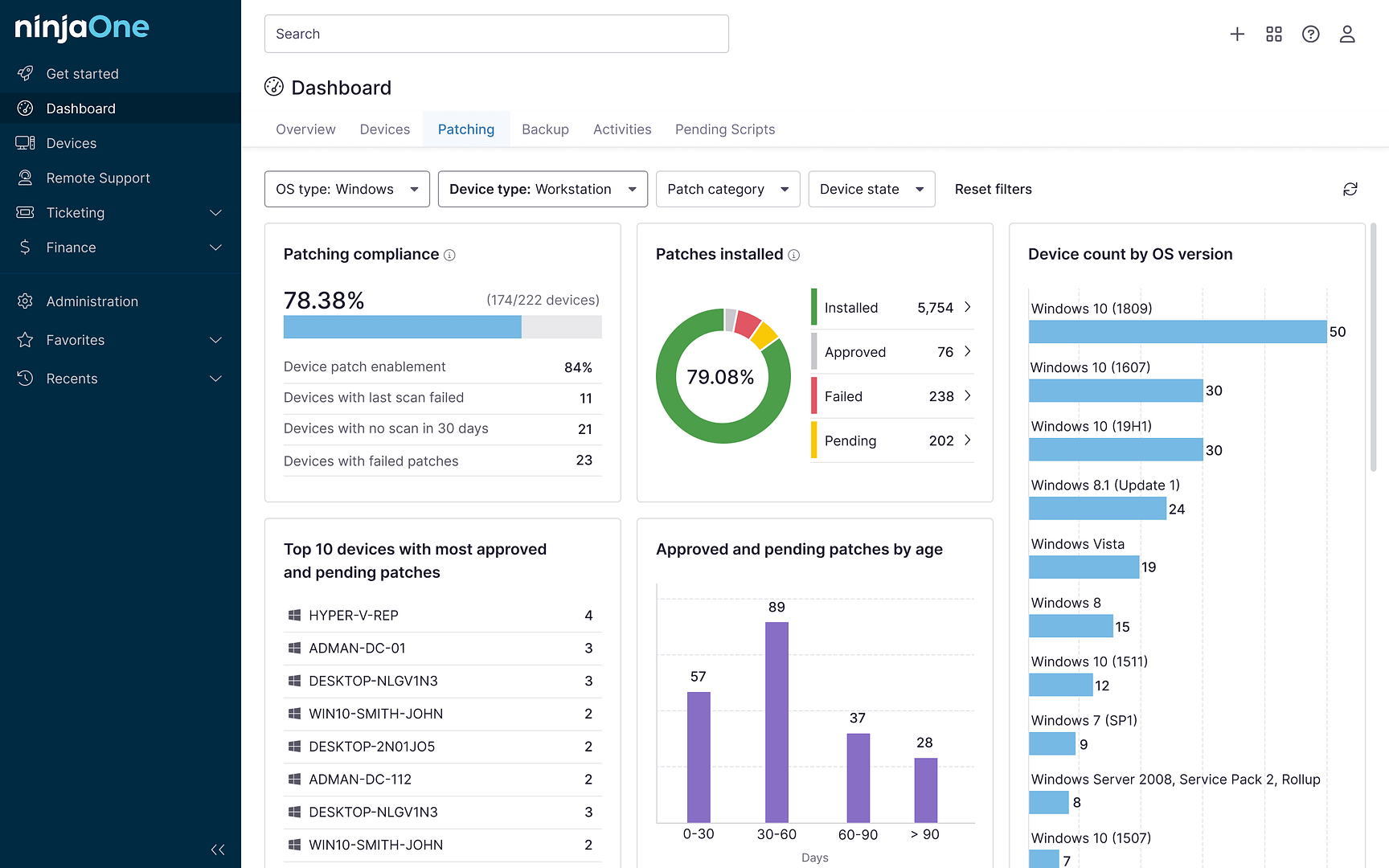
Legitimate svchost.exe processes typically reside in the System32 directory of Windows. Any svchost.exe process located elsewhere could be suspect. Monitoring tools can help identify svchost.exe processes that exhibit unusual behavior such as high network usage or unexpected memory consumption.
Tools and methods to verify the authenticity of svchost.exe processes
- Process Explorer: This free tool provides detailed information about which services each svchost.exe instance is hosting.
- Windows Security Center: Built-in Windows security tools can scan and verify the integrity of running processes, including svchost.exe.
Common signs of svchost.exe-related malware
- Unusual resource consumption: High CPU or memory usage by svchost.exe that doesn’t correlate with known system activities or updates may indicate malicious activity.
- Svchost.exe files running from non-standard locations: Any svchost.exe process executing outside of the C:\Windows\System32 directory should be considered suspicious and possibly malicious.
- Network communications atypical for the services hosted by svchost.exe: Unexpected network activity, such as frequent data transfers or connections to unfamiliar IPs, can be a sign of malware using svchost.exe to mask its operations.
Should you remove svchost.exe?
Removing svchost.exe is a common misconception that can lead to significant system instability and functionality loss. Svchost.exe is crucial for running vital Windows services, and its removal can disrupt essential operations. It is fundamental to system operations, hosting critical services necessary for the proper functioning of the Windows operating system.
Alternative solutions for addressing svchost.exe-related issues:
- Deep scan: Conduct a full system scan with antivirus software.
- Wash, rinse, reinstall: In extreme cases, virus infections can still necessitate a full format and clean Windows reinstallation.
- Less is more: Use system configuration tools to disable specific services if they are not necessary.
- Stay current: Update Windows to ensure all security patches and performance improvements are applied.
Steps to take if you suspect a malicious svchost.exe process:
- Confirm the file path of the svchost.exe process.
- Run a malware scan using reputable antivirus software.
- Consult with a professional if malware removal or further analysis is necessary.
How to keep svchost.exe secure
- Regular monitoring and updating of security software: Regular monitoring of svchost.exe activities and maintaining up-to-date antivirus software are crucial. Ensure that all Windows updates are applied promptly to mitigate any vulnerabilities that could be exploited in outdated systems.
- System maintenance and software updates: Regular maintenance, including disk cleanups, system scans, and updating software, can help prevent svchost.exe from becoming a gateway for malware.
- Enabling and configuring Windows Firewall: Proper settings in Windows Firewall can help block unauthorized connections to and from svchost.exe processes, enhancing the security of these vital system components.
Using antivirus and anti-malware software for protection
Robust antivirus programs can detect and remove malicious software masquerading as legitimate svchost.exe processes, providing an essential layer of security. At the time of writing, the built-in Windows Defender application is still widely considered to be the best free antivirus/anti-malware solution on the market, even outperforming many premium commercial options.
Securing svchost.exe: Insights and implications
Svchost.exe is a critical system process in Windows, essential for managing multiple background services efficiently. Understanding its functionality helps users optimize their systems and recognize potential issues early.
Maintaining the integrity of svchost.exe is paramount for ensuring a secure and stable operating system. Stay vigilant about where svchost.exe processes are running from, monitor their resource usage, and regularly scan your system to ensure no malicious processes are imitating legitimate svchost.exe instances.